The fall and rise of a spyware empire

The spyware was supposed to be invisible and untraceable. Instead, the company was caught and exposed.
By the time it was a decade old in 2014, the Italian company Hacking Team had a worldwide business in surveillance. Its advanced surveillance technology, called Remote Control System (RCS), was sold to governments including some of the world’s most notorious dictatorships. It was used to surreptitiously steal data from anyone the customer targeted. When researchers finally began to uncover Hacking Team’s activities, the target list included human rights activists and journalists.
In 2015, hackers hit Hacking Team. Data totaling over 400 gigabytes, including emails, invoices, and source code, was publicly released. The company’s own Twitter account, itself hacked, trumpeted the breach.
To the public, the company enabled repressive regimes. To industry colleagues, it was a hacking company that got hacked. Customers began to stay away, and even students were wary of working for it.
Nearly five years later, Paolo Lezzi hopes to revive the disgraced outfit, turning the disaster back into a profitable business.
The new regime
I met Lezzi last week at a high-tech defense and military trade show in Paris. It’s been just under one year since he bought Hacking Team, changed the name, combined it with his own company, and set about the task of bringing the once mighty business back from the dead.
My first question was an obvious one for the head of a spyware company linked to repressive regimes.
“How do you make sure there is no abuse?” I asked.
Lezzi inhaled slowly as he considered the question. He looked up and pointed to a display of machine guns just a few feet away from where we spoke.
“Why does everyone ask us this question, but no one asks them that question?” he said, raising his eyebrows.
Lezzi is the owner of Memento Labs and its parent company, InTheCyber. Memento Labs was formed in March when Lezzi acquired Hacking Team.
That acquisition pulled together the remaining Hacking Team engineers and the research and development team from InTheCyber. The company adopted its new, more low-profile name and began rebuilding. This year it made its public debut at the major surveillance industry conferences ISS World in Prague and Milipol in Paris, where I found him.
“We have completely redesigned,” Lezzi said. “We are developing the best possible tools to support law enforcement.”
“Impossible to uncover”
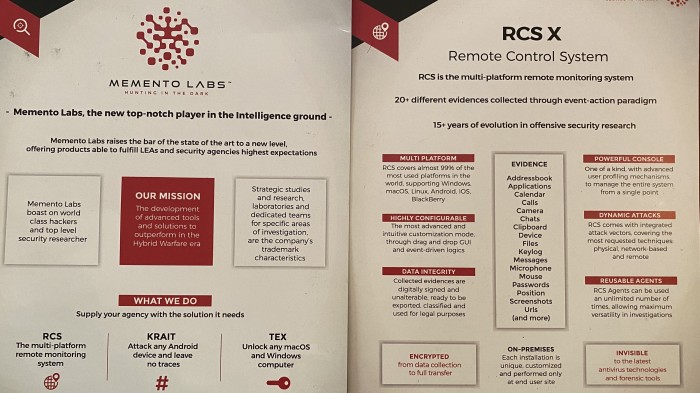
Memento Labs (Slogan: “Hunting in the dark”) sells a variety of impressive snooping tools.
Its KRAIT product allows someone to “attack any Android device and leave no traces,” taking over the device to surveil it with no action required by the target.
The company provides what it calls a “trusted implant” to get KRAIT onto the target’s device, meaning the malware will be delivered from what looks to the victim like a known source. It’s a service “making effortless the social engineering campaign.” KRAIT is a small agent and hides inside legitimate applications.
KRAIT can steal passwords from the target. It can also launch any number of expensive exploits, the highly valued and constantly changing tools that take advantage of digital security vulnerabilities in order to slip inside software and take control. The communications between KRAIT and the attacker’s command and control servers are camouflaged by moving through trusted online services and apps.
“Payloads are never stored on the target devices,” the company says, “making it almost impossible to uncover the existence of the agent and its capabilities.”
When KRAIT takes over your phone, it’s no longer your phone. The device’s location data, microphone, camera, calls, address book, file system, text messages, and more now belong to the hacker who bought KRAIT.
“What’s particularly troubling is that products like KRAIT are designed to silently infect and invisibly surveil even ‘paranoid targets’ who might have a high level of digital security awareness,” says Bill Marczak, a researcher at the University of Toronto’s Citizen Lab who led early research into Hacking Team.
“These products are a match made in heaven for human rights abusers, who are looking for tools to attack an increasingly vigilant civil society.”
The main event
Memento’s flagship product, RCS X, is the latest version of RCS, the highly effective spyware that in 2012 was discovered to be in use against journalists and human rights activists throughout the Arab world and in Washington, DC. Citizen Lab has identified other government users of RCS, including authoritarian regimes from Egypt and Ethiopia to Saudi Arabia and Sudan. It’s been spotted in the wild as recently as last year.
The result of 15 years of development, RCS X offers “invisible” infection of “99% of the most used platforms in the world,” including macOS, Linux, Android, iOS, and BlackBerry. The tool infects any number of targets through the use of exploited security vulnerabilities. One console can manage all the infections and collect encrypted and cryptographically signed data from applications, calendars, messages, passwords, and more.
With RCS X, a hacker can control the microphone and camera, take screenshots, and ultimately gain complete control of a targeted machine.
The spyware has a long history of successful sales and uses—albeit uses that in many cases were caught, despite the promises of invisibility, and ended up contributing to Hacking Team’s demise. It will be key to any future success for Memento Labs.
Faster than the law
Memento will sell only to official law enforcement, intelligence agencies, and militaries. The company asks for and requires permission from Italian export authorities—the same authorities that revoked Hacking Team’s global license in 2016 after evidence emerged that the product was used in countries like Sudan, Saudi Arabia, and Egypt and linked to human rights abuses.
But the laws governing the industry are not good enough, says Marietje Schaake, a former member of the European Parliament who repeatedly raised alarms about surveillance technology being built and sold in Europe. She first stumbled upon the tools during the Arab Spring, a pro-democracy movement in the Middle East, when Hacking Team was implicated in selling spyware like RCS to the Egyptian dictatorship.
“I was not surprised that dictators would do anything to keep their grip on power,” Schaake says. “I was surprised that these tools were coming from democracies.”
Schaake’s decade-long career in the legislative branch of the EU was punctuated by efforts to increase legal accountability and transparency in the surveillance industry to prevent the kinds of abuses that made Hacking Team famous.
“The technology moved faster than laws,” she says. “All the laws governing exports used to come from the security field. There was not a human rights component until after events like the Arab Spring and the murder of Jamal Khashoggi. Italy in particular drags its feet—they are always against restrictions and sanctions. They would rather be ‘pragmatic.’”
Lezzi says Memento Labs now takes a technical step to avoid abuse: the company limits the number of software “agents” sold to governments. It’s the agent that is able to spy on and control a machine.
“If you sell thousands of agents, it could be that it’s not for law enforcement,” Lezzi explains, pointing out that some industry competitors sell exactly that kind of vast and indiscriminate spying capability. He, on the other hand, limits the number of agents sold so that Memento technology is limited to 25 or 50 infections. “It is impossible to go against human rights with only 50 agents,” he says.
However, there is no way for Memento to directly detect abuse by governments that use its surveillance tools, and so the ultimate use of the spyware is outside Lezzi’s control.
Bill Marczak is skeptical that Memento Labs’ safeguards will work, pointing to a 2014 case where the Ethiopian government used Hacking Team’s spyware to target journalists. “Ethiopia’s government had no problem going after journalists and opposition groups with the 50 agents sold by Memento’s predecessor, Hacking Team,” he says.
Indeed, the new advertising material for RCS X also promises that “RCS Agents can be used an unlimited number of times, allowing maximum versatility in investigations”—and, it would seem, few limits on scope.
Rebuilding
Memento faces an uphill battle, not just in reforming its reputation but in gaining a market foothold again. The surveillance industry has many highly capable competitors. Israeli firms in particular are blazing new trails technologically and politically. It’s not easy to compete with a surveillance industry giant the size of Israel’s NSO Group.
Then again, the industry is booming: there have never been so many surveillance and spyware products for sale as there were at this year’s Milipol conference. If there are more industry competitors, there is also more money and greater demand from countries around the world.
Most countries lack the massive budget and cutting-edge capabilities of American intelligence agencies. Memento Labs hopes to build a lucrative business by making up the difference for medium-sized nations that want to realize ambitions in cyberspace on the cheap. Whether the company can avoid the catastrophes that doomed its predecessor is another question entirely.
Deep Dive
Computing
How ASML took over the chipmaking chessboard
MIT Technology Review sat down with outgoing CTO Martin van den Brink to talk about the company’s rise to dominance and the life and death of Moore’s Law.
Why it’s so hard for China’s chip industry to become self-sufficient
Chip companies from the US and China are developing new materials to reduce reliance on a Japanese monopoly. It won’t be easy.
Modernizing data with strategic purpose
Data strategies and modernization initiatives misaligned with the overall business strategy—or too narrowly focused on AI—leave substantial business value on the table.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.