True scale of Bitcoin ransomware extortion revealed
Ransomware is one of the more worrying types of malware to emerge in recent years. It works by restricting access to computer files until a ransom is paid. Victims have included the British National Health Service, the Spanish telecom company Telefonica, the Russian oil giant Rosneft, and many others.
Victims are usually required to pay a Bitcoin ransom equivalent to a few hundred dollars to release their files. Typically, the ransom increases over time until a deadline when the files are supposedly destroyed. Many companies and individuals have had little choice but to pay up.
And that raises an interesting question. How much money have Bitcoin ransomware programs generated for their malicious masters?
Today we get an answer thanks to the work of Mauro Conti at the University of Padua in Italy and a couple of colleagues. These guys have created a database of Bitcoin accounts used by ransomware criminals and added up the ransoms paid into them. The result is a comprehensive analysis of the gains made by cybercriminals in this emerging area of crime.
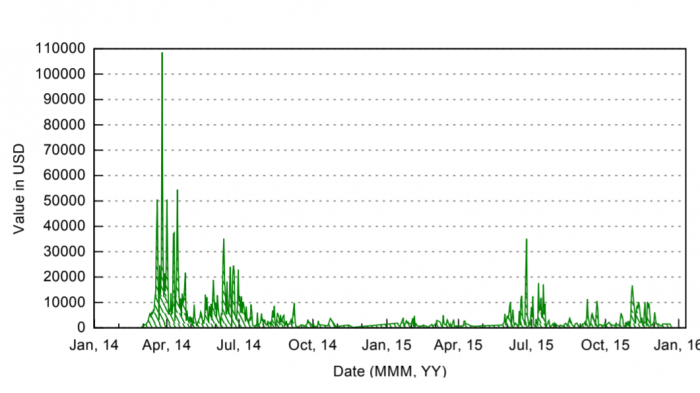
While ransomware can ask for payment in kind of currency, Conti and co focus only on those that ask for Bitcoin payments. That’s because Bitcoin transactions are openly recorded and free to view. So in principle, it should be possible to work out exactly how much each account receives. “Our aim was to accurately measure the USD worth of these payments,” says Conti and co.
The team began by creating a database of Bitcoin accounts associated with this kind of activity since 2013, when the ransomware Cryptolocker became the first to ask for payment in Bitcoin. “We found twenty ransomware that fulfilled our selection criteria, i.e., those ransomware: (i) that used Bitcoin as at least one mode of ransom payment, and (ii) for which at least one Bitcoin address is publicly known,” they explain.
For each species of malware, they provide a useful overview of the way it works and spreads and how it has evolved over time.
Not all payments to these accounts are necessarily ransoms. So Conti and co developed a way to distinguish ransom payments from other types. They do this by looking for payments that correspond to the specific amounts that the malware demands in ransom.
Finally, Conti and co add up all the ransom payments received by each type of malware. Their work reveals the most profitable ransomware but also raises questions about the way these accounts are used and how they can be tracked.
By far the most profitable form of ransomware turns out to be CryptoWall, which began infecting Windows computers in November 2013. It encrypted the files using the RSA-2048 encryption algorithm and then demanded a payment of up to $1,400 to release them.
The malware spread through various vectors, such as download links sent by the Cutwail spam botnet. Some versions of the malware created a unique Bitcoin payment address for each infected user and used the Tor darknet system to provide anonymous links to each victim.
Between its release and December 2015, Bitcoin addresses associated with this malware received $2.2 million in Bitcoin payments and a further $2.3 million in higher-value transactions, which Conti and co suspect may also be ransom payments.
Curiously, the total value of payments received by these Bitcoin addresses was over $45 million. Most of these transactions were not directly linked by Conti and co to ransom amounts. That’s a significant amount of money and raises the obvious question of what it was payment for.
The full ranking of Bitcoin ransomware projects by the US dollar amount they generated is as follows:
Ransomware Bitcoin ransom received USD value
CryptoWall 5,351.2329 2,220,909.12
CryptoLocker 1403.7548 449,274.97
DMA Locker 339.4591 178,162.77
WannaCry 47.1743 86,076.76
CryptoDefense 126.6960 63,859.49
NotPetya 4.0576 9,835.86
KeRanger 9.9990 4,173.12
Interestingly, the WannaCry outbreak received huge media coverage as the malware spread widely. But the attack was foiled by the cybersecurity researcher Marcus Hutchins, who discovered and activated a built-in kill switch that prevented the malware from being more destructive.
“The overall impact (including financial losses) due to WannaCry infection could have been worse … thanks to the early detection of the kill switch, which prevented the infected computers from spreading WannaCry further,” say Conti and co.
The team also discuss other forms of malware that asked for but do not seem to have received any substantial ransoms. These include TeslaCrypt, Hi Buddy!, and KillDisk.
Various other groups have carried out similar analyses and come to similar conclusions. However, Conte and co make their data set publicly available so others can build on it. “The dataset contains a detailed transaction history of all the addresses we identified for every ransomware,” they say.
Cybercriminals use Bitcoin because it provides a seemingly anonymous way of gathering and making payments. However, Bitcoin is pseudonymous rather than anonymous. That means users can protect their identify provided that none of their transactions can be linked to their real identity. But as soon as a single transaction is linked to their personal identification data, then all of their transactions become linked in the same way.
A useful analogy is to authors who publish under a pseudonym. As long as the author’s identity is never linked to any of the pseudonymous articles, he or she remains anonymous. But if it is linked to just one pseudonymous article, it is linked to all of them, and then anonymity is lost.
So pseudonymous protection is a fragile thing. A single transaction that links a Bitcoin account to a personal account can reveal the identity of a cybercriminal. And personal data leaks all the time in web-based transactions.
Last year, we wrote about the imperfections in the anonymity of Bitcoin transactions. That should provide some hope of tracking these criminals.
Conti and co have set this type of investigation as a future goal. “We will attempt to trace how the received ransoms were used and by whom,” they say.
That’s brave and ambitious. But it also raises a question—what are law enforcement agencies doing in the meantime?
Ref: arxiv.org/abs/1804.01341 : On the Economic Significance of Ransomware Campaigns: A Bitcoin Transactions Perspective
Keep Reading
Most Popular
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
What’s next for generative video
OpenAI's Sora has raised the bar for AI moviemaking. Here are four things to bear in mind as we wrap our heads around what's coming.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.