The anatomy of a sextortion spam campaign

The emails all follow the same theme, starting with something like this:
“I’ve been watching you for a while because I hacked you through a trojan virus in an ad on a porn website.”
The attacker goes to profess knowledge of the victim’s passwords, claiming to have evidence of them viewing pornographic websites and perhaps even footage from their webcam.
The email ends with a demand for payment in the form of Bitcoin. Nonpayment will result in the evidence being sent to the victim’s contact list (friends, family, coworkers, and so on), which the attacker has also downloaded.
This is the phenomenon of sextortion, which has burst onto the crime scene in the last year or so. It has spread rapidly because it dramatically simplifies the process of making money via spam.
However, the techniques behind sextortion and the economics that make it effective are poorly understood. Experts would dearly love to know more so they can estimate how much money spammers make in this way, and consequently how widespread the technique is likely to become.
Enter Masarah Paquet-Clouston from the cybersecurity company GoSecure and colleagues from the Austrian Institute of Technology. These folks have studied a huge data set of sextortion emails to better understand how this kind of scam works. Their worrying conclusion is that it is lucrative and likely to become more widespread.
The team say that sextortion emails demanding cryptocurrency payment first appeared in 2018. The scammers send their emails via botnets, such as Necurs or Cutwail. These are global networks of computers infected with malware that send out spam on demand.
This is offered as a service on the dark net. Various researchers have shown that spammers pay botnet owners between $100 and $500 to send a million spam emails. They can even rent botnets at a cost of $10,000 per month, which allows them to send 100 million spam messages.
Conventional spam directs people to websites that sell questionable products such as penis enlargement kits, weight loss schemes, and so on. These sites require a way of procuring, storing, and sending out the goods and a way to take payment via a bank willing to accept or ignore this kind practice.
All that adds up to a significant cost, but one that spammers hope to exceed with revenues. Back in 2008, one group of cyber-crime experts infiltrated a botnet for 26 days and monitored spammers sending 350 million emails for a pharmaceutical product. The result was 28 sales.
This generated a revenue of $2,732, which corresponds to a conversion rate of just 0.00001%. Nevertheless, the experts concluded that by using additional botnets, spammers could generate around $9,500 per day which adds up to $3.5 million per year. Not a bad return.
Sextortion has the potential to be much more profitable, say Paquet-Clouston and co. The reason is that it does not require the spammers to host any kind of e-commerce website, or to procure, store, and ship products of any kind. And cryptocurrency payments are simpler than bank payments and do not require the involvement of a friendly bank.
The researchers first used a cloud-based email filtering service, offered by a company called Excello, to gather a database of sextortion emails sent out during 2018 and 2019.
They used this to pick out emails classified as spam that mentioned Bitcoin and came from an IP address known to be a member of a botnet. The service had prevented all these emails from reaching the recipient. In total, this created a database of 4.3 million sextortion emails in a variety of languages.
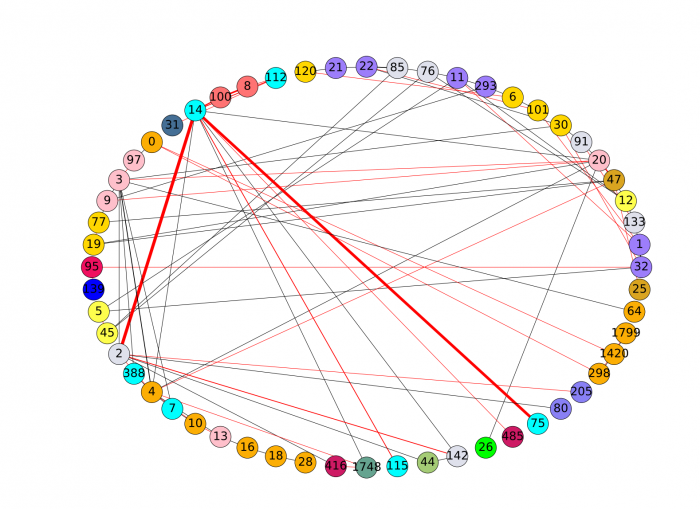
The team then used various data mining techniques to study the email in more detail—for example, by grouping together messages that contained similar threats or used the same Bitcoin payment addresses. Finally, Paquet-Clouston and co studied the different kind of threats and pricing strategies in the emails and examined the Bitcoin accounts to see what happened to the extorted payments.
The results make for interesting reading. Paquet-Clouston and co say that sextortion scammers use different pricing strategies for different languages. “Overall, spammers ask higher amounts, on average, for spams sent in English, Slovenian and Korean and lower amounts, on average, for spams sent in Polish, Italian and Spanish,” they conclude.
Curiously, scammers do not charge more for emails that contain the victim’s password or phone number. “This is surprising considering that these additional elements could make the threat more convincing,” say the researchers. They point out that most of these personal details are gathered from security breach databases that are publicly available. So there is clearly little or no hacking involved.
Furthermore, the scammers do not track the success of these different strategies. Paquet-Clouston and co realized this after noticing that the many sextortion emails in different languages demand payment at the same Bitcoin address. So the scammers could not easily determine which campaign generated this money.
The team also study the Bitcoin accounts that accepted extortion payments. Although these are anonymous, the transactions themselves are completely transparent. “Filtering out unrelated transactions, we conclude that this sextortion scheme generated a lower-bound revenue between $1,300,620 and $1,352,266 for an 11-month period,” say Paquet-Clouston and co.
Most payments appear to be linked to a subset of sextortion campaigns. “Our analytics strongly indicates that a large majority of the financial revenue streams generated by sextortion spam can essentially be attributed to a single real-world entity,” say Paquet-Clouston and co.
That doesn’t imply that all the campaigns were run by a single individual. “It is more likely that botnet infrastructures, which can be rented by spammers, are nowadays designed with financial features that handle the creation of Bitcoin addresses, and potentially handle the financial revenue streams within the Bitcoin ecosystem,” say the team.
That’s interesting work that provides a unique insight into a new form of crime sweeping the globe. And the researchers say that it is likely to continue. “We conclude that sextortion spamming is a lucrative business and spammers will continue to send bulk emails that try to extort money through cryptocurrencies,” they say. “Other schemes, different than sextortion, but involving cryptocurrencies, will likely be developed by spammers, allowing such industry to thrive.”
That’s a clear warning to ordinary people and to the cybersecurity community in general.
Ref: arxiv.org/abs/1908.01051 : Spams meet Cryptocurrencies: Sextortion in the Bitcoin Ecosystem
Deep Dive
Humans and technology
Building a more reliable supply chain
Rapidly advancing technologies are building the modern supply chain, making transparent, collaborative, and data-driven systems a reality.
Building a data-driven health-care ecosystem
Harnessing data to improve the equity, affordability, and quality of the health care system.
Let’s not make the same mistakes with AI that we made with social media
Social media’s unregulated evolution over the past decade holds a lot of lessons that apply directly to AI companies and technologies.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.