How quantum terrorists could bring down the future internet
The first computer virus is widely thought to have been a program called Creeper that infected Apple II computers in the early 1980s. It was written by a 15-year-old high school student in 1981 as a prank. Since then, an entire class of malicious software and activities have emerged that can destroy data or eavesdrop on communication.
One way to combat eavesdropping is to use the rules of quantum physics to protect data. Indeed, there is currently huge investment in designing and testing a quantum version of the internet that will prevent eavesdropping and make communication almost perfectly secure.
But that raises an interesting question. How might malicious actors attack such a quantum internet?
Today, we get a worrying answer thanks to the work of Neil Johnson at George Washington University in Washington, DC, and a few colleagues. These guys have worked out how quantum terrorists could bring the quantum internet to its knees almost instantly and without revealing their identity. More worrying still is that there is no obvious way to counter this new kind of attack.
The team begins their study by creating a mathematical model of the quantum internet. This is a network over which a large number of entangled photons can coexist. For the purposes of the model, Johnson and co think of it as a kind of quantum cloud of entangled photons that people interact with by injecting their own photons carrying quantum information. A key feature of such a system is that the entire entangled internet has its own existence described by a single quantum function.
The question that the researchers wanted to investigate is how a malicious actor might destroy this cloud and the information it contains. One approach would be to simply break the entanglement, which is a famously fragile form of existence. But this would be something of a sledgehammer—a classical attack on a quantum system.
Instead, the team is interested in a much more subtle kind of quantum attack. And they seem to have found it. This kind of attack would involve injecting some random information that becomes entangled with the rest, thereby making the original information impossible to retrieve from the mix.
By itself this does not work. A lone-wolf attacker cannot overwhelm the quantum state with random information. “The correct state (i.e. initial state) can in principle be recovered using purification or distillation schemes,” say Johnson and co.
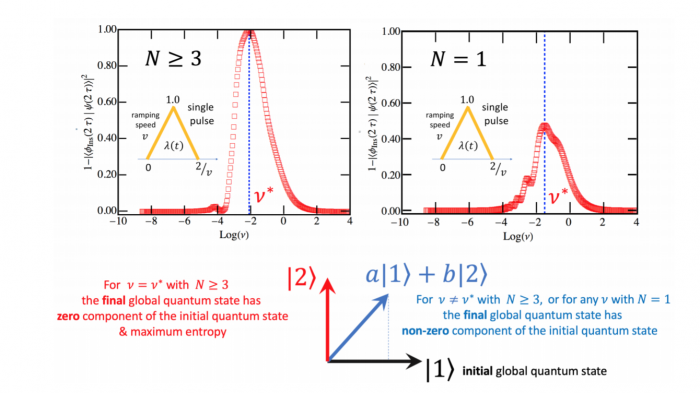
But if quantum terrorists work in unison, an entirely different scenario unfolds. Johnson and co show that if several attackers inject their quantum information into the network at the same instant, they can disrupt the global quantum state. In that case the initial state of the system cannot be retrieved, even in principle.
How many terrorists are needed for this to happen? The shocking conclusion is that it requires only three or more quantum terrorists working in unison. “Our findings reveal a new form of vulnerability that will enable hostile groups of [three or more] quantum-enabled adversaries to inflict maximal disruption on the global quantum state in such systems,” say the team.
What’s more, these attacks will be practically impossible to detect, since they introduce no identifying information; they require no real-time communication, since the terrorists simply agree in advance when to attack; and the attack can be over within a second.
Just how this kind of attack could be countered isn’t entirely clear, although the team has one idea. “A countermeasure could be to embed future quantum technologies within redundant classical networks,” they say.
So instead of the quantum internet existing as a global quantum state, it would instead be a set of connected quantum systems each existing within classical networks and connected together. That would prevent an attack on one part of the network from spreading to other parts.
Indeed, the quantum internet is likely to take this form in its early stages anyway.
Nevertheless, quantum terrorism is a new threat that will give security experts some sleepless nights. And significantly more work will be needed to fully understand the threat and how to mitigate it. As Johnson and his team put it: “Countering this threat properly will require a new understanding of time-dependent quantum correlations in many-body light-matter systems.”
Ref: arxiv.org/abs/1901.08873 : Quantum Terrorism: Collective Vulnerability of Global Quantum Systems
Deep Dive
Computing
How ASML took over the chipmaking chessboard
MIT Technology Review sat down with outgoing CTO Martin van den Brink to talk about the company’s rise to dominance and the life and death of Moore’s Law.
How Wi-Fi sensing became usable tech
After a decade of obscurity, the technology is being used to track people’s movements.
Why it’s so hard for China’s chip industry to become self-sufficient
Chip companies from the US and China are developing new materials to reduce reliance on a Japanese monopoly. It won’t be easy.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.