Crowdsourcing the hunt for software bugs is a booming business—and a risky one
They are the Ubers of the digital security world. Instead of matching independent drivers with passengers, companies like Bugcrowd and HackerOne connect people who like to spend time searching for flaws in software with companies willing to pay them for bugs they find.
This cybersecurity gig economy has expanded to hundreds of thousands of hackers, many of whom have had some experience in the IT security industry. Some still have jobs and hunt bugs in their spare time, while others make a living from freelancing. They are playing an essential role in helping to make code more secure at a time when attacks are rapidly increasing and the cost of maintaining dedicated internal security teams is skyrocketing .
The best freelance bug spotters can make significant sums of money. HackerOne, which has over 200,000 registered users, says about 12 percent of the people using its service pocket $20,000 or more a year, and around 3 percent make over $100,000. The hackers using these platforms hail mostly from the US and Europe, but also from poorer countries where the money they can earn leads some to work full time on bug hunting. (For a profile of a freelance ethical hacker based in the Philippines, see our Jobs of the Future series.)
Code cleaners
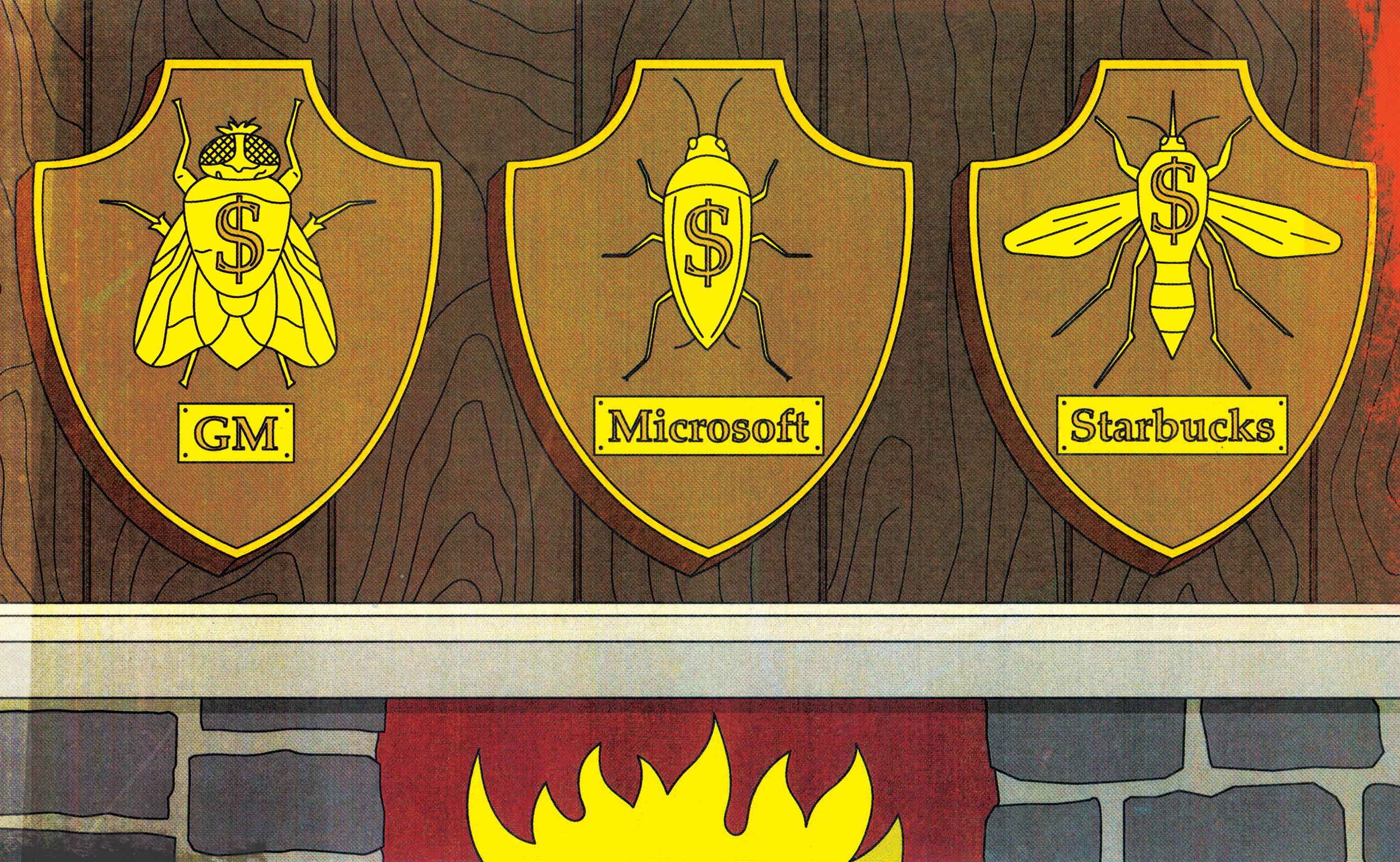
More and more large companies like GM, Microsoft, and Starbucks, are now running “bug bounty” programs that offer monetary rewards to those who spot and report bugs in their software. Platforms like Bugcrowd can help by alerting the hacking community to programs being launched, prioritizing bugs sent on to firms, and handling things like payments.
Richard Rushing, chief information security officer for smartphone maker Motorola Mobility, says he really likes crowdsourcing bug searches because it means lots of eyes are constantly scrutinizing code, and because freelance hunters report software flaws fast in order to scoop up bounties before rivals do.
Moreover, at a time when experts are forecasting that 3.5 million cybersecurity jobs worldwide will be vacant by 2021 because there aren’t enough skilled workers, freelancers can ease some of the strain on internal teams.
Still, the platforms face a couple of big challenges. One is to keep expanding the pool of talented bug hunters. Another is to establish greater legal clarity about what tools and techniques ethical hackers can safely use. Popular tactics such as using injection attacks, which involve inserting code into software applications that could change the way the programs are executed, could potentially lead to prosecution under anti-hacking laws such as America’s Computer Fraud and Abuse Act (CFAA).
There have already been cases where security researchers and reporters have faced possible legal action for unearthing and reporting vulnerabilities in companies’ code. It would take only a couple of high-profile lawsuits to have a chilling effect on the industry.
Hacker uni
To address the talent challenge, the crowdsourcing platforms are publishing far more content to help hackers upgrade their skills and to attract more people to gig work. Bugcrowd just unveiled Bugcrowd University, which offers free webinars and written guides to things like Burp Suite (yes, that’s really the name), which is a graphical tool for testing web applications’ security.
The platform is also working with experienced ethical hackers to help it spot and train promising freelancers. The best recruits are curious, tenacious, and willing to adapt fast. “The technology’s evolving so quickly that it’s often hard to catch up [with it],” explains Phillip Wylie, Bugcrowd’s talent spotter in Dallas.
HackerOne is also publishing more training material and coaches independent bug hunters—who can be quirky and sometimes abrasive characters—in soft skills like how to communicate more effectively with corporate IT departments.
Legal air cover
On the legal front, the platforms are pushing for more “safe harbor” language to be inserted in contracts governing bug bounties. The aim, says Adam Bacchus of HackerOne, is to get companies to be clear that if hackers follow the rules of engagement within reason, they won’t wind up being taken to court.
Bugcrowd has partnered with Amit Elazari, a security researcher whose work has highlighted the need for safe harbor language, to launch an initiative called disclose.io to create a standardized framework for finding and reporting bugs. This would provide explicit authorization for using bug-hunting techniques that would normally be clear violations of provisions in anti-hacking statutes.
It complements a broader push in the US by groups such as the Electronic Frontier Foundation to stop companies from using laws like the CFAA to silence researchers who find serious flaws and disclose them in a responsible manner.
Casey Ellis, Bugcrowd’s founder and chairman, says some other countries, like the UK and Germany, also have strict anti-hacking laws that could be used to stymie ethical hacking.
Such laws are needed to prevent hackers of all kinds from causing havoc. The challenge ahead is to strike a sensible balance between protecting ethical hackers and shielding companies from rogue ones out to cause harm. Getting this right won’t be easy, but given the dire talent shortage in the cybersecurity world, it’s an issue that we urgently need to address.
Update (August 27): This article has been updated to show Amit Elazari's role in launching disclose.io
Deep Dive
Computing
How ASML took over the chipmaking chessboard
MIT Technology Review sat down with outgoing CTO Martin van den Brink to talk about the company’s rise to dominance and the life and death of Moore’s Law.
Why it’s so hard for China’s chip industry to become self-sufficient
Chip companies from the US and China are developing new materials to reduce reliance on a Japanese monopoly. It won’t be easy.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.