Internet Voting Leaves Out a Cornerstone of Democracy: The Secret Ballot
If the risk of hackers meddling with election results is not enough, here’s another reason voting shouldn’t happen on the Internet: the ballots can’t be kept secret.
That’s according to a new report from Verified Voting, a group that advocates for transparency and accuracy in elections.
A cornerstone of democracy, the secret ballot guards against voter coercion. But “because of current technical challenges and the unique challenge of running public elections, it is impossible to maintain the separation of voters’ identities from their votes when Internet voting is used,” concludes the report, which was written in collaboration with the Electronic Privacy Information Center and the anticorruption advocacy group Common Cause.
Thirty-two states and the District of Columbia allow voters to return completed ballots by e-mail, Internet-connected fax machine, or Web portal. In most cases, this option is limited to voters who live overseas or are serving in the military. Utah extends it to voters with disabilities. In Alaska, all voters are free to return their ballots using a Web portal.
When votes are returned via the Internet, it’s technically difficult to separate the voter’s identity from the vote, says Pamela Smith, president of Verified Voting, since the server has to know that identity in order to authenticate the voter and record the vote. In the systems that states are using now, “the authentication typically happens at the same time as the voting process,” she says. That’s problematic. A previous experiment tested giving voters PIN codes, but hackers working with the researchers were able to find those numbers and associate them with voters, says Smith.
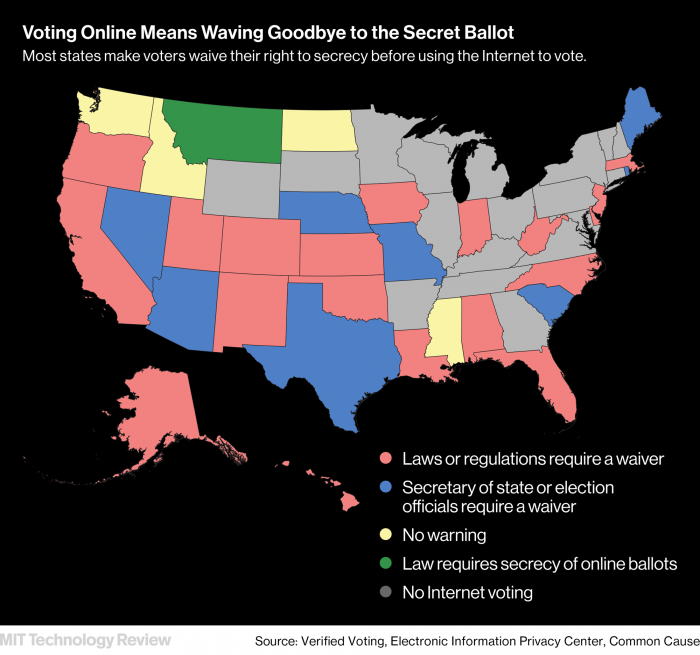
According to the report, issued Thursday, 20 states have laws or regulations requiring that voters who return their ballots via the Internet also waive their right to a secret ballot. In eight states, the secretary of state or election officials require that voters do this even though no laws or regulations require it. Washington, Idaho, North Dakota, and Mississippi don’t warn voters that returning ballots via the Internet also means giving up their secret ballot. Montana requires by law that votes over the Internet be secret, even though that’s not technically feasible.
Smith says the trend toward using the Internet in the voting process could lead to the “erosion” of the secret ballot. “Almost every state has a requirement that there should be secrecy of the ballot,” she says. In order to allow Internet voting, they’ve had to “carve out a special space” that is exempt from that requirement.
Alaska goes so far as to inform voters that if they vote via the Internet, they are not only waiving their right to secrecy but “assuming the risk that a faulty transmission may occur.” Imagine walking into a polling station and seeing a warning like that, says Smith. “How can you field a voting system like that? That’s not right.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.