New Evidence that Cisco Enables Surveillance and Control of China’s Citizens
Cisco is once again supplying networking equipment to the Chinese government for a comprehensive effort to monitor its citizens. This time, it’s for the “Peaceful Chongqing” system, which will is to be the world’s largest surveillance system, with approximately 500,000 cameras aimed at the 12 million inhabitants of Chongqing.
Cisco’s record of helping China create systems that could, and perhaps are, used to oppress its own people is checkered, at best. In 2005, some of its own shareholders tried, and failed, to force the company to consider the potential for its equipment to abet human rights abuses in China and elsewhere.
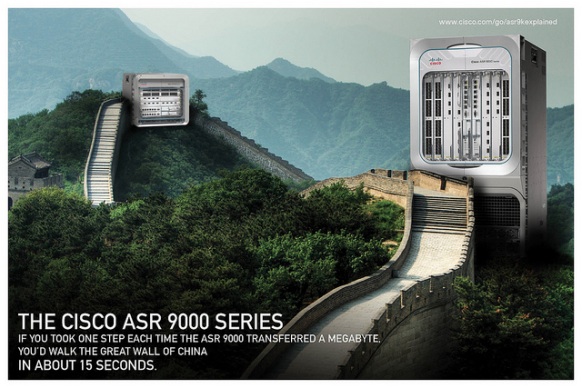
Cisco’s defense against charges of aiding repressive regimes has always been the same: it sells the same networking equipment – mostly routers and switches – to everyone, and doesn’t customize it specifically to aid in human rights abuses. It’s what the company told Congress in 2006, and it appears to be the company’s defense against an ongoing civil suit on behalf of Chinese citizens who were tortured and in some cases murdered by their own government, allegedly after being identified with equipment sold by Cisco.
The problem with Cisco’s defense – that it can’t be held responsible for what governments do with its wares – is that the U.S. government regularly holds companies responsible for what governments do with a company’s products, whatever the stated goal upon date of purchase.
For example, most “dual-use” technologies – items that have both a military and a civilian use – are banned for export under Federal law. This is even true of information technologies. So how does Cisco get away with selling IT to China when that technology could so easily be put to nefarious purposes in the world’s largest non-democratic nation?
Here’s how the Wall Street Journal sums up the “loophole” that Cisco exploits in shipping its wares to China:
The U.S. has prohibited export of crime-control products to China (for instance, fingerprinting equipment) ever since Beijing’s deadly 1989 Tiananmen Square crackdown. But the U.S. restrictions don’t prohibit sale of technologies such as cameras that can be used in many ways—to tame, say, either traffic jams or democracy marches. This loophole troubles some critics.
Internal company memos revealed in 2008 that Cisco is well aware that the Chinese government wants to use its equipment as a tool of repression. That memo even specifically named, as a motivation for buying Cisco’s equipment, the Chinese government’s desire to repress the Falun Gong religious organization whose members were later tortured and murdered by the state.
Suppliers of technology to the Chinese government face a straightforward dilemma: do they miss out on business opportunities in what will soon be the world’s largest economy, knowing that some other supplier will likely be secured, or do they sell their wares anyway, falling back on the defense that almost all information technology is ultimately dual-use?
Google faced a similar dilemma in China, as it first obeyed and then defied official dictates that it censor its search results within the country. Cisco appears to have chosen a different path, as have countless other companies – highlighting, if anything, the extremely unusual nature of Google’s defiance.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.