A Search Engine for the Internet’s Dirty Secrets
Early this week the Austrian security company SEC Consult found that more than three million routers, modems, and other devices are vulnerable to being hijacked over the Internet. Instead of giving each device a unique encryption key to secure its communications, manufacturers including Cisco and General Electric had lazily used a much smaller number of security keys over and over again.
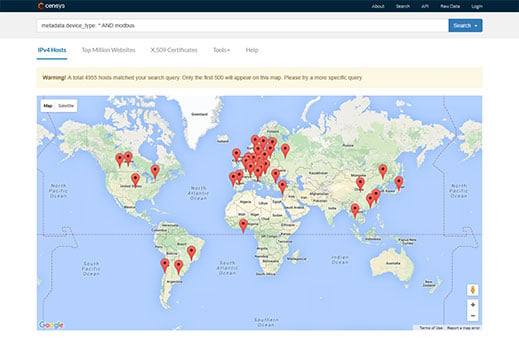
That security screwup was discovered with the help of Censys, a search engine aimed at helping security researchers find the Internet’s dirty little secrets by tracking all the devices hooked up to it. Launched in October by researchers at the University of Michigan, it is likely to produce many more hair-raising findings. Google is providing infrastructure to power the search engine, which is free to use.
“We’re trying to maintain a complete database of everything on the Internet,” says Zakir Durumeric, the University of Michigan researcher who leads the open-source project.
Censys searches data harvested by software called ZMap that Durumeric developed with Michigan colleagues. Every day Censys is updated with a fresh set of data collected after ZMap “pings” more than four billion of the numerical IP addresses allocated to devices connected to the Internet. Grabbing a fresh set of that data takes only hours.
The data that comes back can identify what kind of device responded, as well as details about its software, such as whether it uses encryption and how it is configured. Searching on Censys for software or configuration details associated with a new security flaw can reveal how widespread it is, what devices suffer from it, who they are operated by, and even their approximate location.
Steve Manzuik, director of security research at Duo Security, says that Censys should help make the Internet more secure. His researchers used the tool in their investigation of a major security flaw on computers sold by Dell revealed last week.
Dell had to apologize and rush out remediation tools after Duo showed that the company was putting rogue security certificates on its computers that could be used to remotely eavesdrop on a person’s encrypted Web traffic, for example to intercept passwords. Duo used Censys to find that a Kentucky water plant’s control system was affected, and the Department of Homeland Security stepped in.
Censys was born after Durumeric and colleagues found themselves deluged with requests to run scans to help measure new problems. This March they helped with the response to a major encryption flaw affecting some five million websites including those of Apple, Google, and the FBI (see “Probing the Whole Internet for Weak Spots”).
It has competition in the form of a commercial search engine for security researchers called Shodan, which uses a similar methodology but different software. Durumeric says head-to-head tests show Censys offers significantly better coverage of the Internet and fresher data, making it better suited to measuring and responding to new problems.
John Matherly, founder and CEO of Shodan, says he doesn’t think his coverage is much different, and notes that Shodan currently probes IP addresses in a wider variety of ways than Censys, for example looking specifically for certain types of control system.
Those behind Censys and Shodan can agree that making it easier to ferret out flaws in the Internet should make it more secure. Matherly says his tool has led to over 100,000 industrial control systems being properly secured and helped with the shutdown of numerous servers used by criminals to control malware.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.