How Malware Can Track Your Smartphone Without Using Location Data
Location data is closely guarded by many smartphone users. Nobody wants to think they are being tracked even though they carry the technology to do so in their own pockets.
That’s why the Android and iOS operating system prevent third party apps from accessing location data without the specific permission of the user. But it turns out that malware can track you anyway, without this data.
Today, Yan Michalevsky at Stanford University in California and few pals say that malicious software can determine the position of a smartphone simply by measuring the way it uses the power. “Our approach enables known route identification, real-time tracking, and identification of a new route by only analyzing the phone’s power consumption,” they say.
The technique is straightforward in theory. The idea is that a smartphone’s power usage depends largely on the distance from the nearest base station.
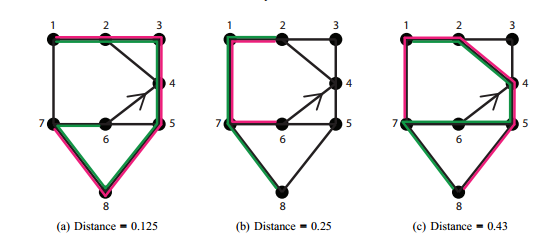
As a user moves, this distance changes, increasing or decreasing the power needed to communicate with a base station. So the power usage profile is strongly correlated with the movement of the phone, or in other words, with the route taken by its owner. Given several different potential routes, the power usage profile should reveal which the user has taken.
There are a couple of caveats. The first is that the user must be moving. The power usage profile is no use in identifying the location of a stationary phone. The second is that this technique distinguishes between different routes which the eavesdropper must have independent knowledge of.
To find out how well this technique works in practice, Michalevsky and co created an Android app called PowerSpy that measures power usage. They then tested it on a number of Nexus 4 devices. In total, they took 43 different power usage profiles on four different routes each about 14 kilometers long.
They then analyzed the power usage profiles to see if they could determine which route had been taken for each. It turned out they could do this with accuracy of 93 per cent.
That’s pretty good, given that there is always noise in the form of power used by other apps throughout the day. That turns out to be of little consequence. Michalevsky and co say it is relatively straightforward to ignore the noise because it is not correlated with the routes. “We showed that applications that read the phone’s ampere meter can gain information about the location of a mobile device without accessing the GPS or any other coarse location indicators,” they say.
So what can be done to prevent this kind of spying? Michalevsky and co have considered a number of ideas. One option is to prevent apps gaining access to power usage data at all, although this is probably overkill. A better option is to give apps access to power usage data other than those involved in radio communication. “We suggest that supplying only measurements of the power consumed by the processors (excluding the power consumed by the TX/RX chain) could be a reasonable tradeoff between functionality and privacy,” they say.
That should be straightforward to implement, if Android or iOS can be bothered.
Michalevsky and co’s work provides an interesting take on privacy and how it can be so easily undermined. Power usage—who’d have thought! It’s also a warning that whatever steps are taken to protect personal data, there will always be ways that it can leak unexpectedly.
Ref: arxiv.org/abs/1502.03182 : PowerSpy: Location Tracking using Mobile Device Power Analysis
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.