The Next Battleground In The War Against Quantum Hacking
Quantum hacking is the latest fear in the world of information security. Not so long ago, physicists were claiming that they could send information with perfect security using a technique known as quantum key distribution.
This uses the laws of quantum mechanics to guarantee perfectly secure communication. And perfectly secure communication is what you get, at least in theory.
The trouble is that in practice the equipment used to carry out quantum key distribution has a number of weaknesses that an eavesdropper can exploit to gain information about the messages being sent. Various groups have demonstrated how quantum hacking presents a real threat to “perfectly secure” communication.
So in the cat and mouse game of information security, physicists have been fighting back by designing equipment that is more secure. Today, Nitin Jain at the Max Planck Institute for the Science of Light in Erlangen, Germany, and a few pals show how the changes still leave the equipment open to attack but at the same time reveal how the next generation of quantum cryptography could be made better.
In quantum key distribution, Alice sends information to Bob encoded in the polarisation of single photons. So she might send a sequence of 0s and 1s as a series of photons polarised horizontally and vertically. Bob can then use this information as the key to a one-time pad for sending information with perfect security. Hence the name quantum key distribution.
An eavesdropper, Eve, can only see the information Alice sends if she knows the directions that correspond to vertical and horizontal. Physicists call this the base of the system.
Without knowing the base, the information the photons carry will seem random. So a key part of the security of quantum key distribution comes from keeping Alice’s base secret.
Just over 10 years ago, hackers found a way for Eve to discover Alice’s base. All Eve has to do is shine a light into Alice’s equipment and measure the polarisation of the reflected photons. These will have bounced off the optical components that determine Alice’s base and so will be polarised in the same way. That gives Eve the crucial information she needs to decode the transmissions without Alice being any the wiser.
Various teams have shown how this approach can hack commercially available quantum cryptography devices, revealing that the claim of perfect security is somewhat overblown.
But the physicists have fought back. One way to stop these kinds of attack is to include a device called an isolator that allows light to travel in one direction but not the other. So Alice can transmit her photons out of the equipment but Eve cannot send photons into it.
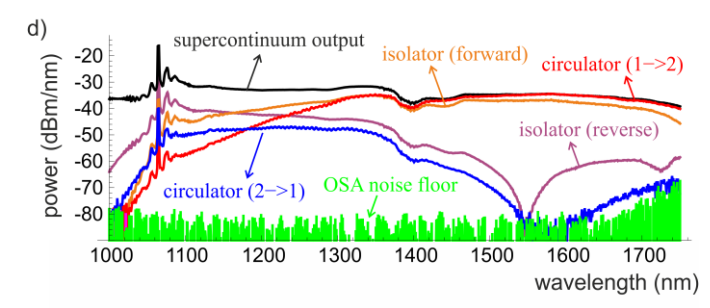
The work that Jain and co have done it to study the optical properties of these devices to see just how secure they are. These guys have tested the optical properties of a number of components used in quantum key distribution, including isolators.
The tests have been straightforward. They send a number of photons towards the device and measure the number that pass through. But crucially, they have done this at a number of different wavelengths between 1000 and 1700 nanometres.
The results are revealing. Telecommunication transmission use wavelengths of around 1550 nanometres. And the isolators Jain and co have measured work well at this wavelength.
But these devices are not so good at other wavelengths. “Even high performance isolators do not have high isolation in other wavelength regions, such as from 1300 to 1400 nanometres, where Eve can easily obtain both laser sources,” they say.
In other words, Eve can still discover Alice’s base using lasers of a different colour.
That will be a worrying discovery for organisations now using quantum key distribution to protect their data, not to mention the companies that sell commercial quantum key distribution equipment.
But all is not lost, say Jain and co. There are still more countermeasures that can protect quantum key distribution from Eve’s attacks at other wavelengths. Instead of using a passive device like an isolator, Alice could use an active device that measures incoming photons in the hope of spotting Eve in action. “If Alice contains a monitoring detector in addition to the isolator, then it would become fairly challenging for Eve to simultaneously circumvent both of these countermeasures,” say Jain and co.
Theorists can help here too. The laws of quantum mechanics guarantee the secrecy of a message provided that the amount of information that leaks out is below some threshold, determined by the specific details of the protocol being used..
In these kinds of attacks, Eve’s gains only a certain amount of information about the secret key. If she gets more than this threshold, she can begin to decrypt any secret messages encoded with it.
The theorists can help here by determining how much information Eve might get from her attacks and raising the threshold accordingly. That increases the security of the system but also makes it considerably slower to send data.
That is an interesting piece of work. Information security specialists have always indulged in a cat and mouse war against attackers. For a short time, these specialists had hoped that quantum key distribution would be the ultimate weapon to bring this war to an end. That hope now looks somewhat premature.
Ref: arxiv.org/abs/1408.0492 : Risk Analysis Of Trojan-Horse Attacks On Practical Quantum Key Distribution Systems
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.