The Perfect Scam
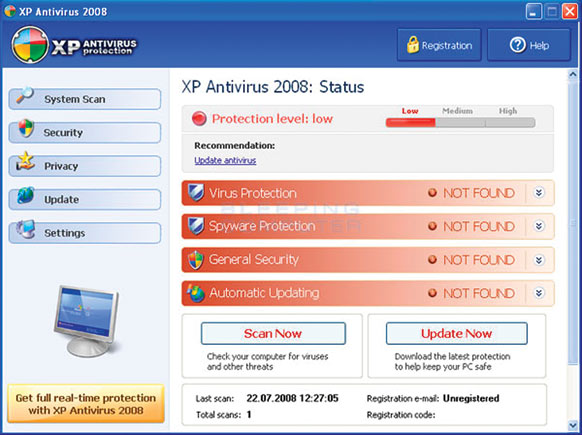
Not long after Prince William and Kate Middleton exchanged vows on April 29, a 1981 wedding portrait of the groom’s late mother, Princess Diana, appeared as one of the top three images for people typing the most popular search term on Google that morning: “royal wedding coverage.” But the link was a trip wire. Fraud artists had finagled a malicious website through Google’s algorithm. The link led to a hacked page on a Web comic book called Kiwiblitz.com, which redirected the browser to another site—one with a domain name from an obscure Australian island territory and hosted in Sweden. That site displayed a realistic-looking program called “XP Anti-Spyware” that issued bogus warnings—Your Computer Is Infected! A few clicks led to a purported solution, for $59.95: a download of a fix that didn’t actually exist.

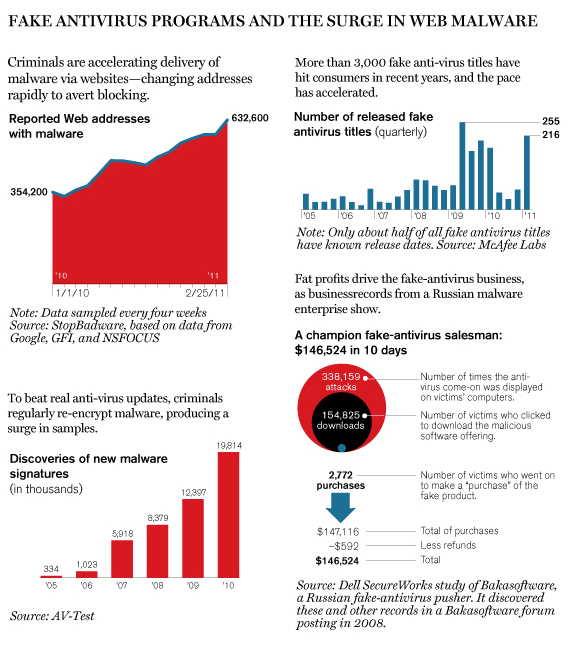
Chalk up another success for what’s generally known as the “fake antivirus” scam. Federal investigators and security experts estimate that its various iterations have extracted at least $1 billion from victims in the past several years, and it has become the most visible manifestation of an overall rise in malicious software, or “malware,” distributed online (see charts below). The damage goes beyond the theft of cash: even if you don’t pull out your wallet, sometimes merely clicking on the bogus come-ons can deliver other forms of malware that may steal your passwords or conscript your computer into a remotely controlled gang called a botnet. Because it generally relies on fooling people into voluntarily installing malware—a strategy called a social-engineering attack—it can wind up infecting even well-maintained machines, both PCs and Macs. “As a human-level act of deception, it is just classically beautiful,” says David Clark, a research scientist at MIT’s Computer Science and Artificial Intelligence Laboratory, who was the Internet’s chief protocol architect in the 1980s.
This threat is a product of nimble technology and a business model that rewards innovation. Con artists have rendered thousands of variants on the fake-antivirus lure in dozens of languages, devised automated means of infecting ordinary websites, and dreamed up many “vectors,” or methods of delivering Web links bearing their nefarious payload. Gamed search results are only one method. Online ads are another vector, as are spam e-mails, links on social networks, and even robo-calls via Skype or telephone advising people to visit websites that belch up the attack. “It’s a really dominant threat to computer users that has persisted over time and continues to evolve and grow,” says Maxim Weinstein, director of StopBadware, a nonprofit in Cambridge, Massachusetts, that helps websites rid themselves of malware hacks and pushes to shut down malicious sites. The success of the scam exposes the flat-footedness of many of the Internet’s major players, which have been unable to coördinate a strategy for dealing with it.
There have been victims in at least 60 countries. “I spent hours cleaning up a system that got infected because an employee clicked on one of these warnings,” says Brian D’Arcangelo, information technology technician at Lynn Community Health Center, in Lynn, Massachusetts. “It’s happening with greater frequency here.” A jewelry maker in Toronto—who wanted only his last name, Moser, used—found his Windows PC locked down with blinking warnings last year after he searched for items related to his trade, so he went ahead and bought the “solution” for $79.95. He had to get the computer cleaned. Searches for terms as mundane as “balloons” have led to attack sites. Apple forums have been lighting up with pleas from customers seeking to extricate themselves from scams like one urging them to buy nonexistent “Mac Defender” software. The mother of Melissa Hathaway, who served as President Obama’s cybersecurity adviser in 2009, clicked to install a fake antivirus product last December. Computer security experts warn that many victims don’t even realize they’ve been scammed.
Economics
The appeal of the bogus antivirus software—often called “scareware”—is rooted in fear. This fraud doesn’t rely on convincing the victim of something preposterous—for example, that a Nigerian prince needs help relocating his money. Instead, the delivery is calibrated to capitalize on the real warnings we’ve all gotten. “People who don’t know exactly what’s going on—and have been [told], ‘Run your antivirus protection, brush your cyber-teeth every day’—are going to be driven to try to respond to that,” says Vint Cerf, a coinventor of the Internet’s original protocols, who is now chief Internet evangelist at Google. The attacks generally come from countries where cyber-crime laws are lax (or unenforced) and treaties obligating coöperation with other nations are not in effect. Many criminal gangs operate networks from Eastern Europe in particular. (Some malware checks to see whether a potential victim’s computer is set for Eastern European locales or has a Russian-language keyboard, whereupon it will gracefully exit.)

It’s easy to see why the fake-antivirus scam is so popular among criminals. The payoff is immediate and the profits large. Someone who steals other kinds of digital booty, like credit card numbers or passwords, must take extra steps to cash in. But a fake antivirus product puts money right into the crook’s pocket. For example, in 2008 the U.S. Federal Trade Commission sued principals of Innovative Marketing, which was incorporated in Belize and at the time maintained offices near Kiev, Ukraine. The FTC said the company hauled in more than $163 million from 2004 to 2008 by tricking consumers into clicking to download fake software with such clever titles as Winfixer, WinAntivirus, Drivecleaner, SystemDoctor, and XP Antivirus 2008. Last year a federal judge in Maryland levied a judgment in that amount against company principals Shaileshkumar “Sam” Jain and Bjorn Daniel Sundin, who were later hit with wire-fraud indictments in federal court in Chicago. They remain at large. A third defendant, James Reno of Amelia, Ohio—who had settled with the FTC—was also indicted; he is accused of running a call center where operators tried to fend off people who complained, though the staff also sometimes provided refunds to irate customers in order to stay off the radar of credit card companies. His attorney did not return messages left by Technology Review.
The damage wrought by this organization may have been even worse than the FTC alleged. A researcher for the security company McAfee was able to determine that Innovative Marketing had some 600 employees and 34 servers disseminating malware, most of them operating from a traditional office complex in Kiev. The corporate empire included divisions that handled credit card payments, the call center in Ohio, and several adult websites that did double duty as vectors for the fake antivirus software. McAfee noted that Innovative Marketing logged 4.5 million orders during an 11-month period in 2008; at $35 per order, the annual revenue apparently neared $180 million. That’s better than the $150 million that Twitter will pull in this year, according to an estimate by the market research firm eMarketer.
Innovative Marketing no longer exists. But that hasn’t slowed the worldwide fake-antivirus business. “There have been multiple malware gangs working rogue antivirus scams consistently over the past five years,” says Eric Howes, research analyst at GFI Software, in Clearwater, Florida. To keep the operations humming, purveyors of this and other forms of malware adapt a business technique used by companies like Amazon: the affiliate model. Just as anyone’s website can include a link to an Amazon purchase form and collect a fee for any sales, antivirus scammers enlist third parties known as affiliates, who can get a fee for each installation—that is, each time someone opens the door to malware by clicking on the false warning—plus a commission on each resulting “sale” of the phony product. One distributor, Avprofit.com, promised on its website that it would pay between $300 and $750 for every 1,000 installations in the United States, Canada, Great Britain, or Australia, where the chance is higher of encountering victims who can afford to pay what the fake warnings demand. Experience required: Avprofit sought hackers with “minimum average 250 installs per day.”
Many of the affiliates do extremely well. SecureWorks, a unit of Dell, analyzed the distribution of a fake antivirus program called Antivirus XP 2008 via an outfit called Bakasoftware, which was based in Russia. According to documents provided by the hacker behind Bakasoftware, who went by the nickname Krab, one of his top affiliates was able to fool 154,825 people into installing copies of malware on their computers in 10 days, with 2,772 victims going on to enter their credit card numbers. If the documents are accurate, Krab’s affiliate scuttled away with $146,524 in that brief period.
Innovation
Affiliates have spawned an impressive body of dark innovation to create new ways of infecting computers over the Web. A key tool is a legitimate website that has been surreptitiously compromised. If you visit such a site, you are often automatically redirected to a site that brings up the flashing warnings, attempting to fool you into clicking approval to download the fake antivirus program. Often, other malware is seeking unpatched holes in common software like Java and Adobe Flash—holes through which it can install other damaging payloads, like malware that steals passwords stored on your computer. This is known as a “drive-by download.”
Remarkable technology underlies the whole process. To maintain a constant supply of infected websites, criminals write code that crawls the Web looking for known vulnerabilities in common publishing platforms like Wordpress or in Web hosting software such as cPanel, says Weinstein. (Every month, his StopBadware organization helps clean up 1,200 websites, a tiny fraction of the hundreds of thousands believed to be infected at any time.) Alternatively, the criminals can use purloined passwords to log in to websites and add malicious code. To make this job easier, botnets do much of the work automatically.
Booby-trapping websites is just one step. The malicious code must avoid detection if those sites are to remain useful to the criminals. To outwit real antivirus programs that are updated daily, the criminals make cosmetic changes to the code—often with simple and widely available encryption tricks. (The malicious code behind the Princess Di image, for example, was much the same as that used in other fake-antivirus scams but was missed by 38 out of 42 real antivirus scanners.) And to keep ahead of the blacklists that security companies and Web companies maintain to block Web addresses known to be housing malicious software, they exploit techniques for rapidly registering and changing thousands of addresses.
A look at one domain registry shows how easy this is. A company in South Korea specializes in selling millions of addresses in the national domain “.cc”—that of the Cocos (Keeling) Islands, an Australian territory. The Korean shop has registered “co.cc.” To this it can add countless numbers of names. For $1,000, in fact, it’ll give you 15,000 of them. It boasts of having 57 million co.cc sites indexed by Google, showing just how easy it can be to reach a broad swath of victims. And free Web hosting services around the world make it easy to press these sites into service.
Vectors
To get their links in front of victims who are likely to see and click on them, antivirus hoaxers need vectors, and they’ve used many: porn sites, online advertisements, search results, software traded on file-sharing sites, and links on Facebook and Twitter. Increasingly, malicious websites using these vectors are created daily or even hourly to keep ahead of efforts to block them and shut them down.
Infecting online advertising is quite simple: the bad guys buy ads and rig them with malicious code or links. According to the FTC, representatives of Innovative Marketing posed as representatives of real companies and organizations—including Travelocity, Priceline, and Oxfam International—and purchased advertisements supposedly on their behalf. Those online ads employed an ingenious variant on location-based targeting. They appeared legitimate when viewed from the IP addresses of the ad network’s employees, but viewers at other addresses were redirected to fraud sites. More recently, according to a report by the security company Websense, infected advertisements—placed by ad networks that had not thoroughly checked out the clients—have shown up on Gizmodo, TechCrunch, and the website of the New York Times.
But search engines might be the predominant vector now, says Stefan Savage, a computer scientist at the University of California, San Diego. The scam artists play a variety of search optimization tricks to fool the algorithms that Google, Bing, and other engines use to determine which Web links to show in response to search requests. Generally, a page on an infected site (such as Kiwiblitz.com) is quietly stuffed with trendy search terms and links to images. Then the malicious players interlink pages—hundreds or thousands of them—so that the search engines’ Web-crawling programs rank the infected page near the top for apparent popularity and relevance. Denis Sinegubko, a malware researcher in Russia, believes that criminals “have managed to hijack search results on the first pages of Google Image search for millions of keywords.” As a result, he estimates, people clicked on poisoned image-search results 15 million times a month this past spring. Google says it has since reduced the number of malicious links in image searches by 90 percent from peak levels, and a spokesman emphasized that it continues to plug holes in its algorithms to head off new methods of attack. Google says that 0.5 percent of searches bring back returns that include at least one known malicious website. This might sound low, but given that Google handles more than a billion searches daily, it means that five million search returns every day bear a malicious link.
When Google identifies a potentially malicious search result after reports by users or security companies, it flags it with warning messages. And if a site has “gamed” the search engine and should not have been delivered in the first place, Google will remove it from the search returns. Google also reveals its list of malicious sites to Internet security companies and Web browser companies, which can issue their own warnings if you try to type in the addresses. “Our response time has gone from weeks or days to hours and even minutes,” says Panayiotis Mavrommatis, a malware researcher at Google.
But the Web industry still hasn’t been able to keep up with the problem. Facebook, for example, blocks its users from accessing websites on Google’s blacklist and those identified internally and from other sources as malicious. Yet it and other social-networking sites, like Twitter, are still major vectors, in part because criminals set up bogus accounts or hack legitimate ones. Some 40 percent of Facebook status updates contain links; of those, 10 percent lead to spam or malicious websites, according to a November report by Websense. Mavrommatis, like other security researchers, admits that the challenge is a tall one. “With the rotation of domains, the URL-based filters become less powerful. And with content-based filters—again, encryption breaks them,” he says. “That is why it is so hard.”
Flying Blind
Researchers say that ending the scourge of fake-antivirus malware—or malware of any other kind—will be nearly impossible unless Web and security companies collect and share more information about everything from the vectors that predominate in a given week to the banks that fraudsters are using to accept payments. Private companies reveal only limited data about breaches on their sites or malicious links in their networks. “There is surprisingly less information in the industry than you might think,” says Michael Barrett, the security chief at the online payment service PayPal.
That’s partly because having proprietary information about malware provides a competitive advantage for Internet security companies. “There has to be more of a community sharing effort, which the security industry is not used to doing,” says Philippe Courtot, CEO of Qualys, a security company. “Since no one company can have a complete view of the attacks and of the vulnerabilities, only a broader and community-driven effort can solve the problem.”
StopBadware is working on a partial solution: a reporting system to which it hopes a critical mass of Internet companies will contribute reports of infected websites. It will vet reports for accuracy, pass the information to Web hosting companies so they can take down the sites, and publicize which hosting companies aren’t cracking down. Increased pressure on those companies could force the criminals to change tactics, adding costs for them.
Another way to hassle the criminals could be to more closely scrutinize the banks that process their credit card payments. Savage suggests that credit card companies and law enforcement need not target many banks to have a big impact. He and colleagues recently studied a random sample of 120 products advertised through spam and determined that 95 percent of their sales went through just three banks, in Azerbaijan, Latvia, and St. Kitts and Nevis, West Indies. Savage believes that a study of payments for fake antivirus software would yield comparable results.
Meanwhile, at any one time, at least several hundred thousand websites—known ones—are distributing malware through fake-antivirus and other scams. “The criminals are doing a better job coördinating their offense than the good guys are doing coördinating our defense,” Weinstein says. That means the bogus flashing warnings—Your Computer Is Infected!—increasingly reflect the truth.
David Talbot is Technology Review ‘ s chief correspondent.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.