Sponsored
IT security starts with knowing your assets: Asia-Pacific
A new, well-organized breed of hacker and the fast-evolving nature of technology are forcing organizations to consider multiple ways of minimizing threat exposure.
In association withCortex Xpanse by Palo Alto Networks
On the best of days, securing the networks, devices, and data of NTUC Enterprise is no easy task. The Singapore-based cooperative consists of nine business units, from food services to insurance, and serves more than 2 million customers in nearly 1,000 locations.

When the 2020 coronavirus pandemic hit, it forced many of NTUC’s employees to work from home, often on unsecured networks and personal devices. Almost instantly, the company’s “traditional defenses like corporate firewalls disappeared,” recalls Ian Loe, chief technology officer for NE Digital, the digital unit of NTUC.
IT security starts with knowing your assets
A perfect example of remote-work security challenges occurred when an NTUC employee accidentally downloaded malware onto a laptop he was using to access corporate files by plugging in a personal USB drive. “We received a security alert right away, but the remediation was tough,” recalls Loe. “We actually had to send a cybersecurity staffer to the employee’s house on a motorbike to retrieve the computer for investigation. In the past, we could protect the network by simply cutting off the employee’s laptop access. But when an employee is working from home, we can’t take the chance of losing any data over the internet.”
Welcome to the new cybersecurity threat landscape, where 61% of organizations are increasing cybersecurity investment in the work-from-home pandemic era, according to a 2021 Gartner CIO Agenda survey. Remote workers rely on cloud computing services to do their jobs, whether it’s corresponding with co-workers, collaborating on projects, or joining video-conferencing calls with clients. And when information technology (IT) teams, now at a physical remove, are not responsive to their needs, remote workers can easily shop for their own online solutions to problems. But all that bypasses normal cybersecurity practices—and opens up a world of worry for IT.
Yet for many regions of the world, remote work is just one of many factors increasing an organization’s exposure to cybersecurity breaches. The Asia-Pacific region is no exception, where 51% of organizations surveyed by MIT Technology Review Insights and Palo Alto Networks report having experienced a cybersecurity attack originating from an unknown, unmanaged, or poorly managed digital asset.
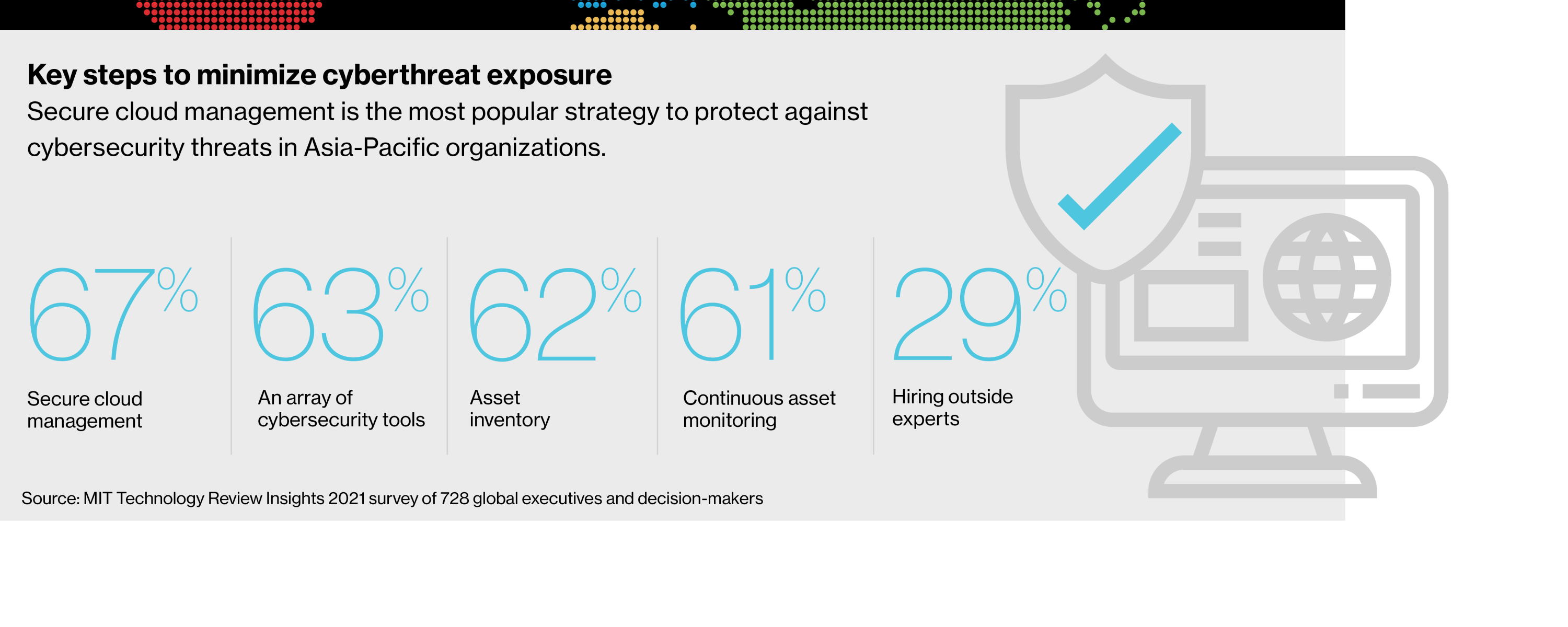
Conducting a full inventory of internet-connected assets and rebooting cybersecurity policies for today’s modern remote work environment can mitigate risks. But organizations must also understand the cybersecurity trends and challenges that define their markets, many of which are unique to organizations operating in the Asia-Pacific.
To better understand the challenges facing today’s security teams in this region, and the strategies they must embrace, MIT Technology Review Insights and Palo Alto conducted a global survey of 728 respondents, 162 from the Asia-Pacific. Their responses, along with the input of industry experts, identify specific security challenges in today’s IT landscape and provide a critical framework for safeguarding systems against a growing battalion of bad actors and fast-moving threats.
The vulnerabilities of a cloud environment
The cloud continues to play a critical role in accelerating digital transformation. And for good reason: cloud technologies offer substantial benefits, including increased flexibility, cost savings, and greater scalability. Yet, cloud environments are responsible for 79% of observed exposures, compared with 21% for on-premises assets, according to the 2021 Cortex Xpanse Attack Surface Management Threat report.
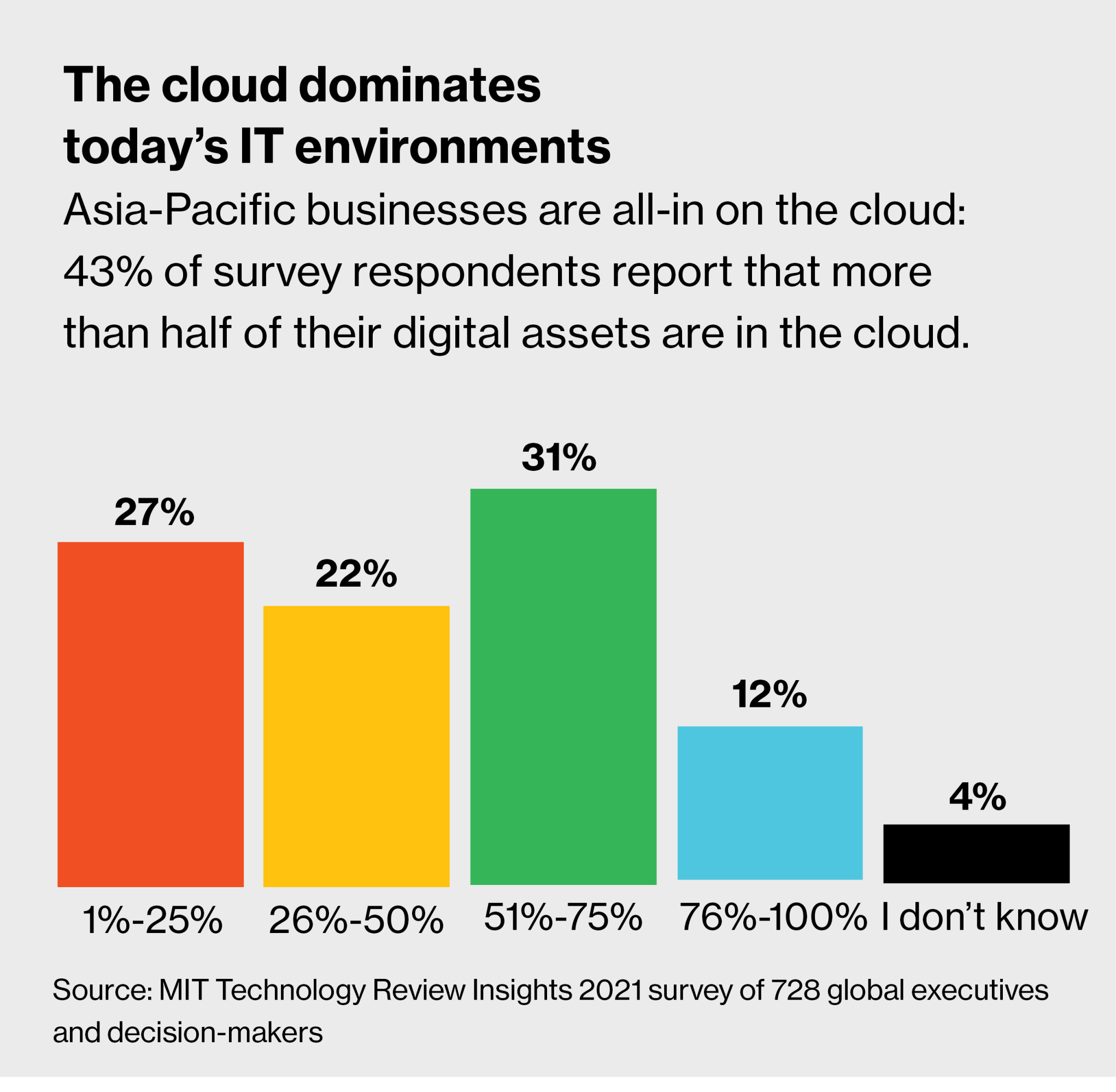
That’s a key concern, given that nearly half (43%) of Asia-Pacific organizations report that at least 51% of their operations is in the cloud.
One way cloud services can compromise an organization’s security posture is by contributing to shadow IT. Because cloud computing services can be easily bought and deployed, Loe says, “procurement power moves from a company’s traditional finance office to its engineers. With nothing more than a credit card, these engineers can buy a cloud service without anyone keeping track of the purchase.” The result, he says, is “blind spots” that can thwart IT efforts to protect a company’s attack surface— the totality of possible entry points. After all, adds Loe, “We can’t protect what we don’t know exists—that’s an extreme reality today.”
Biocon’s Agnidipta Sarkar agrees. “Without the bureaucracy associated with procuring IT capabilities, shadow IT can run rampant,” says Sarkar, group chief information security officer (CISO) at the Indian pharmaceutical company. “Unless an organization really plans for digital resilience, unplanned and uncontrolled growth of digital assets can escape the focused governance that information security requires.”
The exponential growth of interconnected devices is also challenging organizations to secure their cloud infrastructures. “Many people are not aware that internet-of-things devices such as sensors are actually computers, and that they’re powerful enough to be used to launch bots and other types of attacks,” warns Loe. He cites the example of smart locks and other mobile applications that allow employees to unlock and open doors—and allow hackers to gain unauthorized access to corporate networks.
While cloud services and interconnected devices raise universal cybersecurity issues, Asia-Pacific organizations face additional challenges. For instance, Loe points to the varying degrees of cybersecurity maturity among the region’s countries. “We have countries like Singapore, Japan, and Korea which rank high in terms of cyber maturity,” he says. “But we also embody Laos, Cambodia, and Myanmar, which are at the lowest end of maturity. In fact, some government officials in these areas still use free Gmail accounts for official communication.” Some vulnerable countries have already been used as launchpads for attacks on neighbors, Loe says.
Another factor that distinguished some Asia-Pacific countries from other regions in the world was an unpreparedness to quickly pivot to remote work in the early months of the pandemic. According to Kane Lightowler, vice president of Cortex, Palo Alto’s threat detection platform division, organizations behind in their digital transformation efforts “had to prioritize business continuity first and foremost,” allowing cybersecurity to take a back seat. Unfortunately, he adds, “many of these companies still have not caught up to performing business in a secure and compliant manner. Only now, in 2021, are they starting to prioritize security again.”
Download the full report.
Find out what organizations in other regions of the world are doing to understand and counter today’s cyberthreats.
This content was produced by Insights, the custom content arm of MIT Technology Review. It was not written by MIT Technology Review’s editorial staff.
Deep Dive
Computing
Inside the hunt for new physics at the world’s largest particle collider
The Large Hadron Collider hasn’t seen any new particles since the discovery of the Higgs boson in 2012. Here’s what researchers are trying to do about it.
How ASML took over the chipmaking chessboard
MIT Technology Review sat down with outgoing CTO Martin van den Brink to talk about the company’s rise to dominance and the life and death of Moore’s Law.
How Wi-Fi sensing became usable tech
After a decade of obscurity, the technology is being used to track people’s movements.
Algorithms are everywhere
Three new books warn against turning into the person the algorithm thinks you are.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.