A multimillion-dollar criminal crypto-mining ecosystem has been uncovered
Cryptocurrencies have become magnets for illicit activities such as theft and fraud. But one of less-reported crimes is the use of stolen processing power to mine currencies such as Bitcoin and Monero. The proceeds of this theft can then be exchanged for real currency, reaping vast rewards for malicious actors.
How extensive are these illicit mining networks and how much money do they make?
Today, we get an answer thanks to the work of Sergio Pastrana at the Charles III University of Madrid in Spain and Guillermo Suarez-Tangil at King’s College London. These guys have analyzed these networks in detail for the first time and say they generate much richer pickings than anyone had imagined.
Pastrana and Suarez-Tangil estimate that this kind of crime has generated more than $50 million. And they go on to reveal how the cybercriminals carry out their crimes. “To the best of our knowledge, this paper presents the largest systematic study of malicious binary-based crypto-mining,” they say.
There are essentially two ways to steal processing power. The first is to set up a web page incorporating a script that hijacks the computer’s CPU. Unsuspecting visitors to the site suddenly find their CPU overloaded and their fans blasting.
Of course, the ruse can be stopped by closing the page that is responsible. Cybersecurity experts have analyzed this kind of activity by counting the web pages that contain this kind of malware and estimating how many times they are visited and for how long.
The second method is much harder to investigate. It consists of crypto-mining malware, often buried in legitimate code, that users unsuspectingly install and run on their computers.
This malware is designed to be hard to detect. Some malware switches off whenever the user opens the task manager, so the evidence of its activity is hard to see. Other types only switch on when the CPU is idle, on the assumption that the user must be away from the device.
Pastrana and Suarez-Tangil focus their study on this second type of cryptomining malware, also known as binary-based malware. And their analysis is revealing.
First, some background. Cryptocurrency mining is the process that encrypts a record of transactions so that it cannot be changed or tampered with later. This encryption must be strong enough to make the record almost impossible to reengineer.
That requires significant processing power, which is a valuable resource. So miners are rewarded for their efforts with small amounts of cryptocurrency. That’s why the process is called mining: because it creates new currency.
The mining process is so intensive that miners often join together in pools. In this way, they combine their processing power and then share out the rewards, which are paid into cryptocurrency wallets.
Cryptomining malware does all this using the processing power of its host computer. It generally works by downloading open-source mining software that does the encrypting, signing into a mining pool and then transferring any rewards into a wallet.
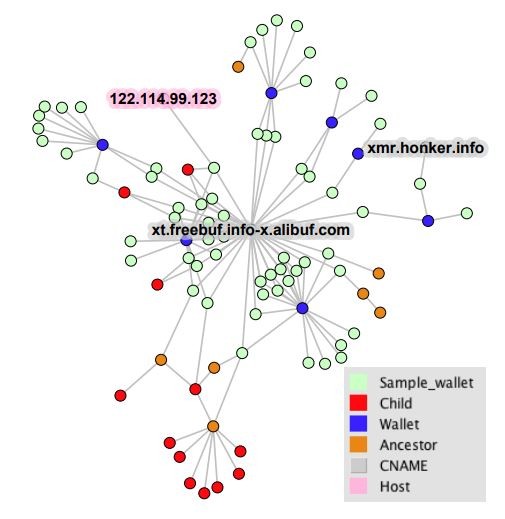
But it is exactly this process that has allowed Pastrana and Suarez-Tangil to analyze the activity of these malicious miners. The malicious code contains details of the pools it connects to and the wallets that funds are paid into.
The researchers simply extract this information on a massive scale. They collected 1 million examples of crypto-mining malware operating between 2007 and 2018. They then analyzed the code involved and ran the malware in a protected sandbox environment to see what it did.
That revealed the pools most often involved in illicit crypto-mining. It also revealed the wallets, allowing the researchers to see how much cryptocurrency each had received. “We then analyze publicly available payments sent to the wallets from mining-pools as a reward for mining, and estimate profits for the different campaigns,” they say.
The results of this analysis makes for interested reading. The researchers find that Monero is by far the most popular cryptocurrency for criminals and that the scale of their activity is staggering. Pastrana and Suarez-Tangi say that more than 4.3% of all the Monero cryptocurrency in circulation is the result of criminal activity.
And it is a profitable business. Exchange rates for cryptocurrencies have varied hugely over time. Since there is no way to know when criminals converted their gains, Pastrana and Suarez-Tangi have had to estimate them. But even with conservative estimates, the proceeds are large.
“Our profit analysis reveals campaigns with multi-million earnings,” they say. Indeed, the total amount mined in this way is around $56 million over the last 10 years. And most of this appears to have been gained by a relatively small number of actors. “One of the main reasons of the success of this criminal business is its relatively low cost and high return of investment,” say the researchers.
Stopping this illicit activity is not easy, either. During their research, Pastrana and Suarez-Tangi reported illicit wallets to the largest mining pools in the hope they would be banned. But they ran up against two problems. First, some non-cooperative pools refused to ban wallets linked to crypto-mining malware. Second, some successful illicit crypto-mining campaigns used several pools at the same time, making them more resilient to takedown operations.
One countermeasure seems to work well, however. Every now and again, cryptocurrency authorities make changes to the algorithms used to mine the currency. When this happens, the mining software has to be updated.
That’s not a problem for legitimate miners. But illicit miners have to find a way to update the malware they have distributed around the web. That’s not such an easy task.
Monero changed its algorithms twice in 2018. “In each change, about 73% and 90% of the campaigns ceased their operations,” say Pastrana and Suarez-Tangil.
That’s interesting work that lifts the lid on a hugely profitable but largely unreported criminal activity. It also suggests an effective way to crack down on it by regularly updating mining algorithms. It’ll be interesting to see how the cryptocurrency community reacts.
Ref: arxiv.org/abs/1901.00846 : A First Look at the Crypto-Mining Malware Ecosystem: A Decade of Unrestricted Wealth
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.