There’s a new way to break quantum cryptography

The great promise of quantum communication is perfect privacy: the ability to transfer a message from one point in the universe to another in such a way that the very laws of physics prevent an eavesdropper from listening in.
For hackers, that kind of promise is like a red flag to a bull. Since the first commercial quantum cryptography systems became available in the early 2000s, people have repeatedly attempted to bring them down—with significant success. The attacks have ruthlessly exploited imperfections in the equipment used to send quantum information. In doing so, hackers have shown that even if the laws of physics offer perfect security, equipment can never be perfect. And these imperfections create loopholes that can be exploited.
Quantum physicists were forced to respond quickly, developing new protocols that do not depend on equipment. So-called device-independent quantum cryptography offers perfect security even when the equipment is less than perfect. At least in theory.
But the frightening truth about implementing quantum cryptography is that somebody, somewhere may always be found to have overlooked something important. And this oversight will enable a hack.
Today, Xiao-Ling Pang and colleagues at Shanghai Jiao Tong University in China say they’ve found one of those overlooked factors. Thanks to that discovery, the team has managed to hack device-independent quantum cryptography with a frighteningly high success rate.
First some background. Most quantum encryption systems encode information using photons. Alice sends the photons to Bob, who measures them to reveal the information.
This process relies on the fact that measuring the quantum properties of a photon always changes the information it carries. So if any eavesdropper is tuning in, Alice and Bob can spot Eve’s presence by the changes she introduces to the original message. If they find evidence of eavesdropping, they begin again. Indeed, they keep re-sending the data until they can be sure nobody has overheard it.
Of course, Alice can’t use this technique to send a private message, because it’s only possible to detect Eve after she has listened in. Instead, Alice uses it to send Bob a key—a one-time pad—that he can use to encrypt a message and send it over a classical channel. A one-time pad is provably secure, provided nobody else knows the key.
Various cybersecurity researchers have found ways to hack this kind of system. A shortcoming they’ve exploited is that the data is often encoded in the polarization of a photon: a vertically polarized photon might encode a 1 and a horizontal polarization a 0.
One hack is to shine a high-powered laser into the equipment so that it reflects off the polarizers inside. The reflections reveal the orientation used to polarize and encode the outgoing photons. And that reveals the code. To counter this, physicists have developed ways to prevent these reflections.
Enter Pang and colleagues, who say they’ve found an entirely new way to attack quantum communication that doesn’t rely on reflections. The new technique hinges instead on an effect called injection locking. This is a method of changing the frequency of a laser by injecting photons with a different seed frequency into the lasing cavity. Provided the difference in frequency is small, the laser eventually resonates with the seed frequency.
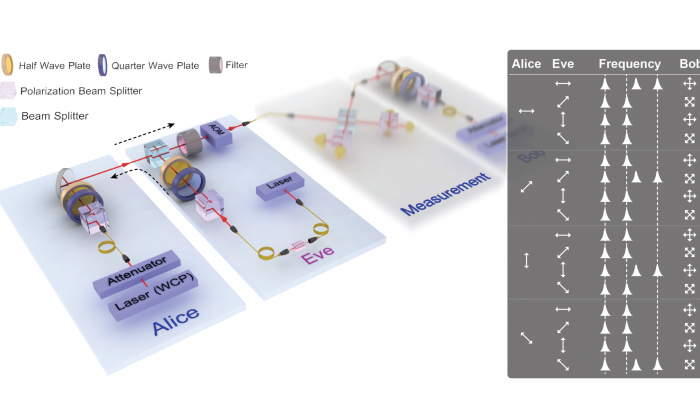
Pang and co inject photons into Alice’s laser so that they change the output frequency. But this only works if Pang’s photons can pass through the polarizer into the lasing cavity. To ensure that this happens, Pang and co inject four photons, each with a different orientation—horizontal, vertical, and plus or minus 45 degrees. They then wait to see whether this changes the frequency of Alice’s outgoing photon. If the frequency is altered, then the polarization of the incoming photon must have matched the outgoing one.
And that reveals the code without measuring the polarization of the outgoing photon. Pang and co then change the frequency of this photon back to the intended frequency and send it on to Bob, who is none the wiser.
Voilà! A hack that reveals the quantum information to Eve without Alice or Bob’s knowledge.
Pang and co say they’ve tested the approach with remarkable results. “We demonstrate that Eve can control Alice’s source by forcing her laser resonant at a designed frequency,” they say. “We obtain a hacking success rate reaching 60.0%.”
That’s interesting work that outlines yet another step in the cat-and-mouse game of quantum hacking.
Obviously, the next step is to find ways to prevent injection locking, and Pang and co have made the first attempts. They say an obvious countermeasure is to use devices known as isolators, which allow photons to travel in one direction but not the other.
However, these devices are by no means perfect. They usually allow photons to travel in one direction but merely reduce the number that can travel in the other.
Pang and co include isolators in their setup that reduce the transmission of unwanted photons by up to 3 decibels. This reduces the hacking success rate to 36%, which they describe as “still considerably high information leakage.”
Of course, it’s not hard to think of other ways to reduce the effectiveness of this kind of attack. But there is a bigger message here: that flaws in device-independent quantum cryptography are still coming to light. “The main message we would like to deliver here is that there may exist many other physical loopholes,” say Pang and co.
That’s an important message. Various companies now offer commercial quantum cryptography services with the promise of privacy beyond that achievable with classical systems. This kind of work is likely to give them, and their customers, some sleepless nights.
Ref: arxiv.org/abs/1902.10423 : Hacking Quantum Key Distribution via Injection Locking
Deep Dive
Computing
How ASML took over the chipmaking chessboard
MIT Technology Review sat down with outgoing CTO Martin van den Brink to talk about the company’s rise to dominance and the life and death of Moore’s Law.
How Wi-Fi sensing became usable tech
After a decade of obscurity, the technology is being used to track people’s movements.
Why it’s so hard for China’s chip industry to become self-sufficient
Chip companies from the US and China are developing new materials to reduce reliance on a Japanese monopoly. It won’t be easy.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.