The real reason America is scared of Huawei: internet-connected everything
There was a time when the world’s two great superpowers were obsessed with nuclear weapons technology. Today the flashpoint is between the US and China, and it involves the wireless technology that promises to connect your toaster to the web.
The two countries are embroiled in a political war over the Chinese telecommunications company Huawei. The Americans have recently stepped up long-standing criticisms, claiming the tech giant has stolen trade secrets and committed fraud, and that it has ties to the Chinese government and its military.
The company denies the charges and has sought to defend its record on privacy and security. Meanwhile, US allies including Great Britain, New Zealand, Australia, Canada, Germany, and Japan have all either imposed restrictions on Huawei’s equipment or are considering doing so, citing national security concerns.
Behind the headlines, though, the spat is also about the coming wave of networking technology known as 5G, and who owns it.
Here are five things you need to know about the technology and its role in the tensions.
1. What is 5G?
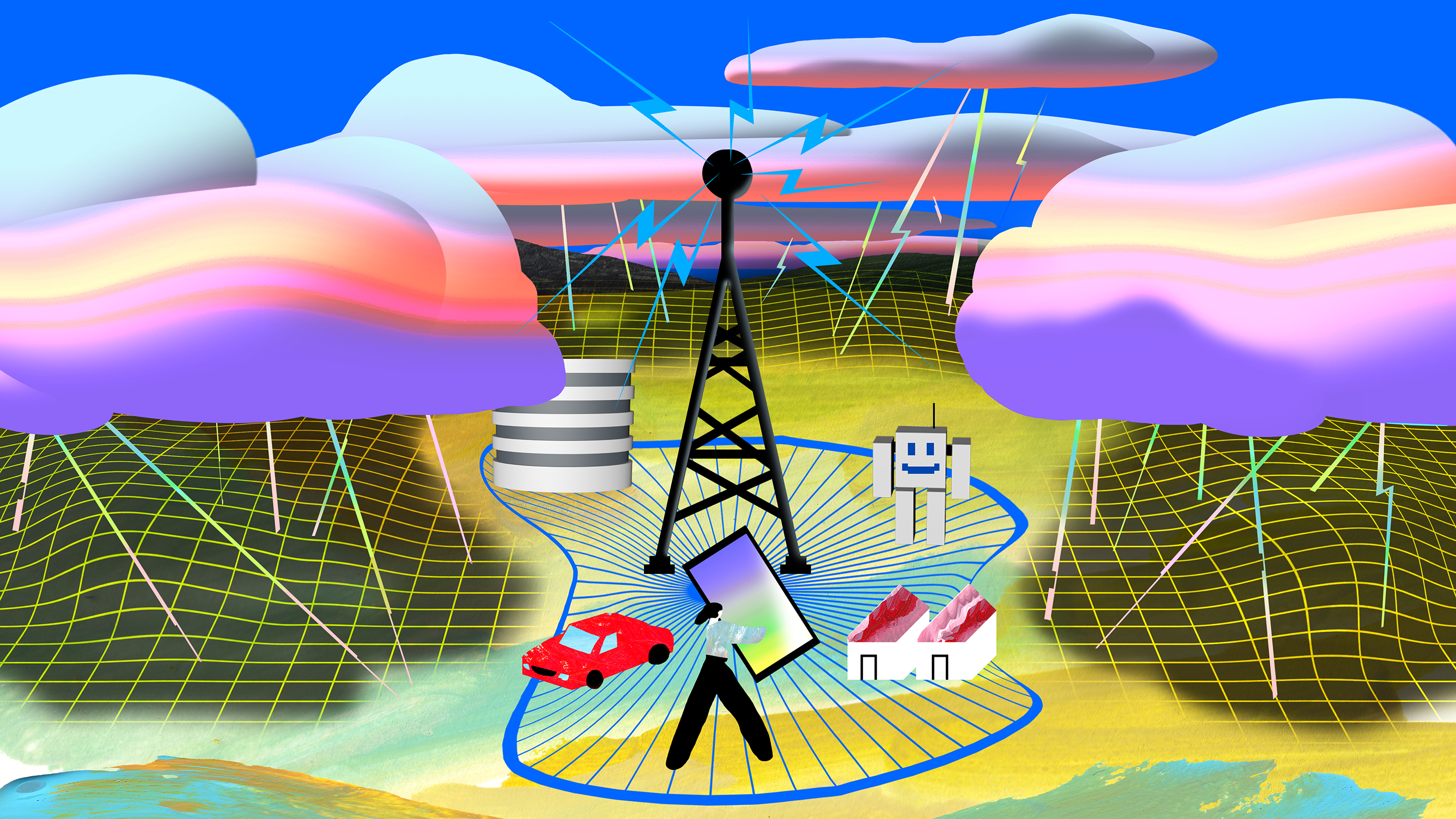
Rather than a protocol or device, 5G refers to an array of networking technologies meant to work in concert to connect everything from self-driving cars to home appliances over the air. It’s expected to provide bandwidth of up to 20 gigabits per second—enough to download high-definition movies instantly and use virtual and augmented reality. On your smartphone.
The first 5G smartphones and infrastructure arrive this year, but a full transition will take many more years.
2. Why is it better?
5G networks operate on two different frequency ranges. In one mode, they will exploit the same frequencies as existing 4G and Wi-Fi networks, while using a more efficient coding scheme and larger channel sizes to achieve a 25% to 50% speed boost. In a second mode, 5G networks will use much higher, millimeter-wave frequencies that can transmit data at higher speeds, albeit over shorter ranges.
Since millimeter waves drop off over short distances, 5G will require more transmitters. A lot of them, sometimes just a few dozen meters apart. Connected devices will hop seamlessly between these transmitters as well as older hardware.
To increase bandwidth, 5G cells also make use of a technology known as massive MIMO (multiple input, multiple output). This allows hundreds of antennas to work in parallel, which increases speeds and will help lower latency to around a millisecond (from about 30 milliseconds in 4G) while letting more devices connect.
Finally, a technology called full duplex will increase data capacity further still by allowing transmitters and devices to send and receive data on the same frequency. This is done using specialized circuits capable of ensuring that incoming and outgoing signals do not interfere with one another.
3. What are the security risks?
One of 5G’s biggest security issues is simply how widely it will be used.
5G stands to replace wired connections and open the door for many more devices to be connected and updated via the internet, including home appliances and industrial machines. Even self-driving cars, industrial robots, and hospital devices that rely on 5G’s ever-present, never-lagging bandwidth will be able to run without a hiccup.
As with any brand-new technology, security vulnerabilities are sure to emerge early on. Researchers in Europe have already identified weak spots in the way cryptographic keys will be exchanged in 5G networks, for example. With so many more connected devices, the risk for data theft and sabotage—what cybersecurity folks call the attack surface—will be that much higher.
Since 5G is meant to be compatible with existing 4G, 3G, and Wi-Fi networks—in some cases using mesh networking that cuts out central control of a network entirely—existing security issues will also carry over to the new networks. Britain’s GCHQ is expected to highlight security issues with Huawei’s technology, perhaps involving 4G systems, in coming weeks.
With 5G, a layer of control software will help ensure seamless connectivity, create virtual networks, and offer new network features. A network operator might create a private 5G network for a bank, for instance, and the bank could use features of the network to verify the identities of app users.
This software layer will, however, offer new ways for a malicious network operator to snoop on and manipulate data. It may also open up new vectors for attack, while hardware bugs could make it possible for users to hop between virtual networks, eavesdropping or stealing data as they do.
4. Can 5G be made secure?
These security worries paint a bleak picture—but there are technical solutions to all of them.
Careful use of cryptography can help secure communications in a way that protects data as it flows across different systems and through virtual networks—even guarding it from the companies that own and run the hardware. Such coding schemes can help guard against jamming, snooping, and hacking.
Two research papers offer a good overview of the risks and potential solutions: 5G Security: Analysis of Threats and Solutions (pdf); Security for 5G Mobile Wireless Networks (pdf).
“If you do it correctly, you will actually have a more robust network,” says Muriel Médard, a professor who leads the Network Coding and Reliable Communications Group at MIT.
5. Why is Huawei’s 5G causing so much concern?
As the world’s biggest supplier of networking equipment and second largest smartphone maker, Huawei is in a prime position to snatch the lion’s share of a 5G market that, by some estimates, could be worth $123 billion in five years’ time.
Stalling the company’s expansion into Western markets could have the convenient side effect of letting competitors catch up. But there are also legitimate security concerns surrounding 5G—and reasons to think it could be problematic for one company to dominate the space.
The US government appears to have decided that it’s simply too risky for a Chinese company to control too much 5G infrastructure.
The focus on Huawei makes sense given the importance of 5G, the new complexity and security challenges, and the fact that the Chinese company is poised to be such a huge player. And given the way Chinese companies are answerable to the government, Huawei’s apparent connections with the Chinese military and its cyber operations, and the tightening ties between private industry and the state, this seems a legitimate consideration.
But the ongoing fight with Huawei also goes to show how vital new technology is to the future of global competition, economic might, and even international security.
Deep Dive
Computing
How ASML took over the chipmaking chessboard
MIT Technology Review sat down with outgoing CTO Martin van den Brink to talk about the company’s rise to dominance and the life and death of Moore’s Law.
How Wi-Fi sensing became usable tech
After a decade of obscurity, the technology is being used to track people’s movements.
Why it’s so hard for China’s chip industry to become self-sufficient
Chip companies from the US and China are developing new materials to reduce reliance on a Japanese monopoly. It won’t be easy.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.