For safety’s sake, we must slow innovation in internet-connected things

Smart gadgets are everywhere. The chances are you have them in your workplace, in your home, and perhaps on your wrist. According to an estimate from research firm Gartner, there will be over 11 billion internet-connected devices (excluding smartphones and computers) in circulation worldwide this year, almost double the number just a couple of years ago.
Many billions more will come online soon. Their connectivity is what makes them so useful, but it’s also a cybersecurity nightmare. Hackers have already shown they can compromise everything from connected cars to medical devices, and warnings are getting louder that security is being shortchanged in the stampede to bring products to market.
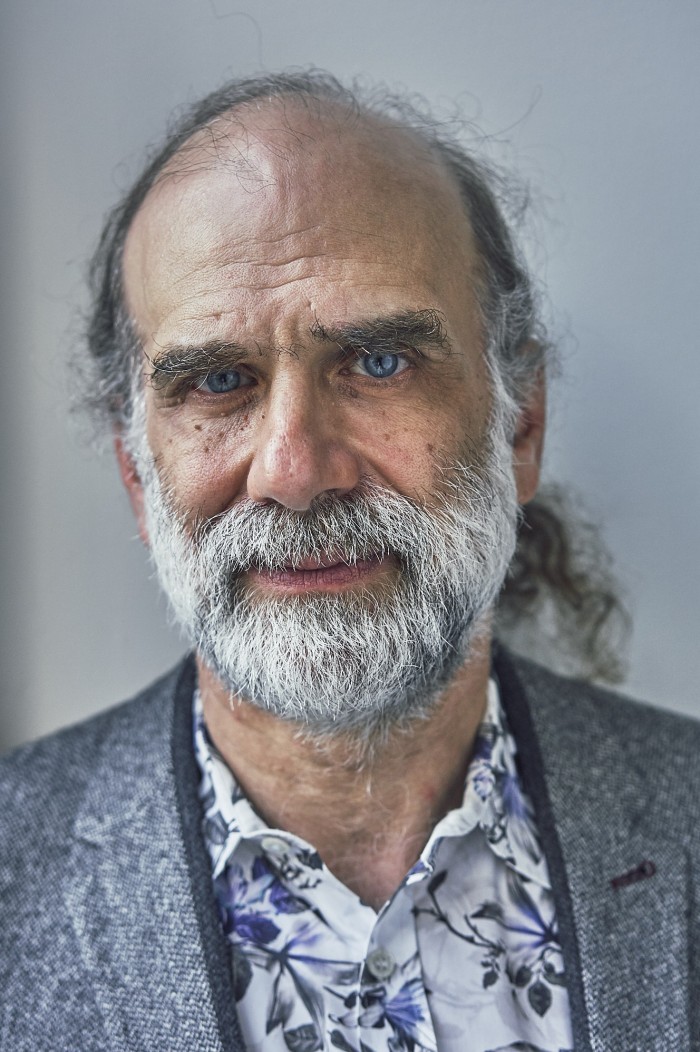
In a new book called Click Here to Kill Everybody, Bruce Schneier argues that governments must step in now to force companies developing connected gadgets to make security a priority rather than an afterthought. The author of an influential security newsletter and blog, Schneier is a fellow at the Berkman Klein Center for Internet and Society at Harvard University and a lecturer in public policy at the Harvard Kennedy School. Among other roles, he’s also on the board of the Electronic Frontier Foundation and is chief technology officer of IBM Resilient, which helps companies prepare to deal with potential cyberthreats.
Schneier spoke with MIT Technology Review about the risks we’re running in an ever more connected world and the policies he thinks are urgently needed to address them.
The title of your book seems deliberately alarmist. Is that just an attempt to juice sales?
It may sound like publishing clickbait, but I’m trying to make the point that the internet now affects the world in a direct physical manner, and that changes everything. It’s no longer about risks to data, but about risks to life and property. And the title really points out that there’s physical danger here, and that things are different than they were just five years ago.
How’s this shift changing our notion of cybersecurity?
Our cars, our medical devices, our household appliances are all now computers with things attached to them. Your refrigerator is a computer that keeps things cold, and a microwave oven is a computer that makes things hot. And your car is a computer with four wheels and an engine. Computers are no longer just a screen we turn on and look at, and that’s the big change. What was computer security, its own separate realm, is now everything security.
You’ve come up with a new term, “Internet+,” to encapsulate this shift. But we already have the phrase “internet of things” to describe it, don’t we?
I hated having to create another buzzword, because there are already too many of them. But the internet of things is too narrow. It refers to the connected appliances, thermostats, and other gadgets. That’s just a part of what we’re talking about here. It’s really the internet of things plus the computers plus the services plus the large databases being built plus the internet companies plus us. I just shortened all this to “Internet+.”
Let’s focus on the “us” part of that equation. You say in the book that we’re becoming “virtual cyborgs.” What do you mean by that?
We’re already intimately tied to devices like our phones, which we look at many times a day, and search engines, which are kind of like our online brains. Our power system, our transportation network, our communications systems, are all on the internet. If it goes down, to a very real extent society grinds to a halt, because we’re so dependent on it at every level. Computers aren’t yet widely embedded in our bodies, but they’re deeply embedded in our lives.
Can’t we just unplug ourselves somewhat to limit the risks?
That’s getting harder and harder to do. I tried to buy a car that wasn’t connected to the internet, and I failed. It’s not that there were no cars available like this, but the ones in the range I wanted all came with an internet connection. Even if it could be turned off, there was no guarantee hackers couldn’t turn it back on remotely.
Hackers can also exploit security vulnerabilities in one kind of device to attack others, right?
There are lots of examples of this. The Mirai botnet exploited vulnerabilities in home devices like DVRs and webcams. These things were taken over by hackers and used to launch an attack on a domain-name server, which then knocked a bunch of popular websites offline. The hackers who attacked Target got into the retailer’s payment network through a vulnerability in the IT systems of a contractor working on some of its stores.
True, but these incidents didn’t lead to loss of life or limb, and we haven’t seen many cases involving potential physical harm yet, have we?
We haven’t. Most attacks still involve violations of data, privacy, and confidentiality. But we’re entering a new era. I’m obviously concerned if someone steals my medical records, but what if they change my blood type in the database? I don’t want someone hacking my car’s Bluetooth connection and listening to my conversations, but I really don’t want them to disable the steering. These attacks on the integrity and availability of systems are the ones we really have to worry about in the future, because they directly affect life and property.
There’s been lots of discussion in the US this year about cyber threats to critical infrastructure like power grids and dams. How serious are these?
We know that at least twice, Russian hackers have turned off power to bits of Ukraine’s grid as part of a broader military campaign. We know that nation-state hackers have penetrated systems at some US power companies. These hacks have been exploratory ones and haven’t caused damage, but we know it’s possible to do so. If there are military hostilities against the US, we should expect these attacks will be used. And the US will use them against our adversaries, just as we used cyberattacks to delay the nuclear programs in Iran and North Korea.
What implications does all this have for our current approach to computer security, such as issuing patches, or fixes, for software flaws?
Patching is a way of regaining security. We produce systems that aren’t very good, then find vulnerabilities and patch them. That works great with your phone or computer, because the cost of insecurity is relatively low. But can we do this with a car? Is it okay to suddenly say a car is insecure, a hacker can crash it, but don’t worry because there will be a patch out next week? Can we do that with an embedded heart pacemaker? Because computers now affect the world in a direct, physical manner, we can’t afford to wait for fixes.
But we already have very strict security standards for software that’s used in sensitive cyber-physical domains like aviation, don’t we?
Right, but it’s very expensive. Those standards are there because there’s already strong government regulation in this and a few other industries. In consumer goods, you don’t have that level of safety and security, and that’s going to have to change. The market right now doesn’t reward secure software at all here. As long as you, as a company, won’t gain additional market share because of being more secure, you’re not going to spend much time on the issue
So what do we need to do to make the Internet+ era safer?
There’s no industry that’s improved safety or security without governments forcing it to do so. Again and again, companies skimp on security until they are forced to take it seriously. We need government to step up here with a combination of things targeted at firms developing internet-connected devices. They include flexible standards, rigid rules, and tough liability laws whose penalties are big enough to seriously hurt a company’s earnings.
But won’t things like strict liability laws have a chilling effect on innovation?
Yes, they will chill innovation—but that’s what’s needed right now! The point is that innovation in the Internet+ world can kill you. We chill innovation in things like drug development, aircraft design, and nuclear power plants because the cost of getting it wrong is too great. We’re past the point where we need to discuss regulation versus no-regulation for connected things; we have to discuss smart regulation versus stupid regulation.
There’s a fundamental tension here, though, isn’t there? Governments also like to exploit vulnerabilities for spying, law enforcement, and other activities.
Governments are certainly poachers as well as gamekeepers. I think we’ll resolve this long-standing tension between offense and defense eventually, but it’s going to be a long, hard slog to get there.
Your book largely focuses on the US. Do you think it will take the lead here?
I focus on the US because it’s where the major tech companies are located and it’s the regime I know best, but I do talk about Europe a fair bit as well. The European Union is the regulatory superpower on this planet right now. I think it’s going to advance further and faster than the US. In the US, I look more to the states, and specifically Massachusetts, New York, and California.
I also think there will be international treaties and norms that put some of our connected infrastructure off limits to nation-state cyberattacks, at least in peacetime. We urgently need action at all levels now, from local to international. My biggest fear is that there will be a cyber disaster, and that governments will rush headlong to implement measures, without a lot of thought, that won’t solve the problem.
Deep Dive
Computing
How ASML took over the chipmaking chessboard
MIT Technology Review sat down with outgoing CTO Martin van den Brink to talk about the company’s rise to dominance and the life and death of Moore’s Law.
How Wi-Fi sensing became usable tech
After a decade of obscurity, the technology is being used to track people’s movements.
Why it’s so hard for China’s chip industry to become self-sufficient
Chip companies from the US and China are developing new materials to reduce reliance on a Japanese monopoly. It won’t be easy.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.