Sponsored
Containing the Career Impact of Cybercrime
in partnership withHewlett Packard Enterprise and FireEye
Sony Pictures Entertainment, the U.S. Office of Personnel Management, Bangladesh Bank, the State of Texas, Ashley Madison, Target: these are a few of the organizations where top or senior-level executives have resigned or been fired in the wake of fallout from major cybersecurity breaches. So should executives everywhere worry about their careers in light of increasingly damaging and sophisticated attacks?
Security industry experts say that the nature and complexity of today’s cyberattacks are beyond the scope of even the largest companies. “It seems unreasonable to expect companies to prevent every sophisticated attack, especially targeted attacks by state actors,” notes Kevin Mandia, CEO of FireEye, a global cybersecurity company.
A recent study by FireEye indicated that 2015 saw a rise in the number of disruptive attacks, in which hackers hold information for ransom, delete critical data, post sensitive company information on the Internet, or add malicious code to a source-code repository. The research also uncovered an increase in the bulk export of personally identifiable information (PII) from targeted companies by Chinese cybercriminals.
Such breaches are hitting corporations where it hurts the most: the bottom line. Bangladesh Bank, which recently experienced a breach resulting in the loss of a staggering $81 million, is just one example of the potential scope of the risk today.
In many such cases, the cybercriminals are never caught or prosecuted because it’s so difficult to track them down. Underground networks of sophisticated hackers can launch an attack from anywhere in the world, using other countries and even other companies to hide what they’re doing, says Arthur Wong, senior vice president and general manager, Hewlett Packard Enterprise (HPE) Security Services. All too often, company executives are held accountable instead.
Often, the CIO or CISO of a midsize—or even a large—company lacks the same level of resources that hackers have. As a result, “it’s an unfair fight, and you can’t make them responsible for it,” Wong says. But that doesn’t mean that companies and shareholders won’t hold executives responsible, he adds.
Breaches are Inevitable, Career Consequences are Not
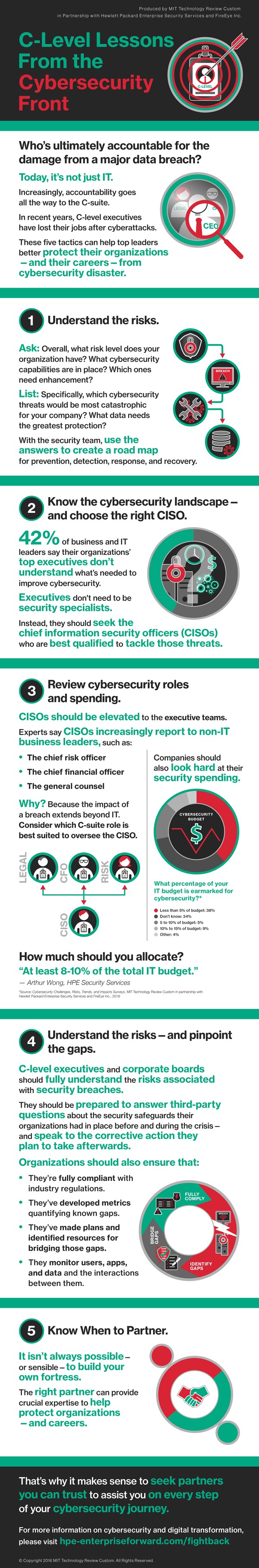
Battling the hackers may seem like a lost cause when some can penetrate major financial institutions and government agencies with seemingly relative ease. Yet with the right preparation, executives from CISOs to board members can help mitigate damage from breaches, even if they can’t prevent them entirely. Following are five tactics for protecting your organization—and your career—from cybersecurity disaster.
1. Create a Risk Profile
Survey Results
Cybersecurity Challenges, Risks, Trends, and Impacts
Produced by MIT Technology Review Custom in Partnership with Hewlett Packard Enterprise Security Services and FireEye Inc.
Every industry, and every organization, faces different security risks. Begin by assessing your organization’s risk level and what capabilities are in place for preventing and responding to an attack, including budget and staff. That knowledge will serve as a road map for creating cybersecurity prevention, detection, response, and recovery plans.
After that, it’s a matter of objectives. Mandia recommends identifying six or seven types of events that you believe would be catastrophic for your company. Next, determine what your organization is doing to combat those threats, whether it’s mitigating the risk of people stealing credit-card data or preventing somebody from hacking into the CEO’s email account. The latter would warrant providing higher levels of security for C-level accounts than those for lower-level employees. “We work with companies to figure out what are your assets that matter most, so you can build a secure enclave around those,” Mandia says.
2. Engage the CEO
More than 42 percent of the business and IT leaders who participated in a February 2016 survey indicated that senior executives in their companies didn’t understand the amount of time and resources needed to mitigate risk and minimize threat exposure, while 16 percent couldn’t gauge executive awareness. (MIT Technology Review Custom conducted the Cybersecurity Challenges, Risks, Trends, and Impacts Survey in partnership with HPE and FireEye.)
“CEOs need to have a much more active role in understanding what is being done, and the level of diligence that is occurring in their organizations, to protect against cyberattacks,” Wong notes. Even if C-level executives don’t actually make the decisions that lead to security breaches, they may well ultimately shoulder the blame.
CEOs shouldn’t, however, be expected to become security experts: that’s the job of the CISO. Instead, “the CEO’s goal is to make sure they hire the best person they can, one who can best implement a plan for the company’s risk profile,” Mandia says.
3. Elevate Cybersecurity Roles and Spending
A growing number of CISOs today report to executives outside the IT department, Wong says. “We see many CISOs reporting to a risk leader, if there is one in the company, or to the CFO, or even to legal,” he says. The trend reflects an increasing understanding that security is no longer just an IT function, because the potential damage from security breaches extends well beyond IT. “Breaches can impact the business, the market capitalization of the company, the brand,” Wong says.
Beyond elevating the CISO’s role, many companies need to boost their investments in security technology and personnel. Wong advises that organizations allocate at least 8 to 10 percent of their total IT budgets to security, but acknowledges that many still spend less.
The Cybersecurity Challenges, Risks, Trends, and Impacts Survey reached a similar conclusion. Fully 38 percent of the 225 business and IT leaders surveyed spent less than 5 percent of their IT budgets on cybersecurity, with just 15 percent estimating such spending at 5 to 10 percent. Only 9 percent reported allocating 10 to 15 percent of their IT budgets for cybersecurity, and just 4 percent estimated spending more than 15 percent. Most of the rest didn’t know what their organizations spent on cybersecurity, a clear indicator that maybe it’s time to find out.
4. Understand the Risks and Ramifications—and Pinpoint the Gaps
CIOs, CEOs, and other corporate officers may wonder whether they need lawyers to represent them in the case of a breach. And, in fact, some law firms offer breach-preparedness services focused on helping executives understand what they need to know before, during, and after a breach, Wong says.
Still, CIOs, CISOs, and other executives typically don’t get dragged into court as witnesses following a breach. “Currently, it is more the norm that there is no lawsuit—or if there is, it’s settled before any sort of trial occurs,” Mandia says. “The advice that I give to boards is: if something bad happens to your organization in cyberspace, you want to be postured to withstand any third-party inspections.” That means answering detailed questions from investigators about the security program and efforts an organization had in place before and during an incident—and being able to discuss the corrective action they plan to take afterwards.
Wong recommends that organizations focus on ensuring that:
- Their companies are in compliance with industry regulations.
- Their boards and executives fully understand the risks associated with security breaches.
- They have developed metrics quantifying known gaps.
- They have instituted plans and made resources available for bridging those gaps.
Specifically, organizations must know where their critical data is and how it’s secured. They must continually assess risks, and they must identify and raise the awareness of their high-risk users. And, of course, they must vigilantly monitor users, applications, and data—and the interactions between them.
5. Seek Expert Partners
It isn’t always sensible, or possible, to build and maintain your fortress alone. An experienced partner can make the job easier by, for instance, providing expert assistance with risk assessment and transformation plans.
“We help people step through how to meet the objectives of their cybersecurity programs, and we respond to virtually every security breach that matters,” says Mandia of FireEye, whose six global operations centers provide constant detection and response to more than 4,400 customers. “That gives you a vantage point of what technology works and doesn’t work as promised, and what the threats actually are today. If there’s a whole bunch of breaches in a certain industry, we can advise very relevant threat intelligence.”
HPE helps clients assess risk, build, architect, design, and implement resilient systems and infrastructure; for those seeking more, it can manage security operations entirely. The company maintains 10 security operations centers worldwide, with 5,000 security professionals serving 10,000 clients. As Wong puts it: “There’s a shortage of security skills and security knowledge around the world, and we help protect customers from threats out there better than they can protect themselves.”
Ultimately, choosing the right partner can help senior executives and their boards navigate cybersecurity challenges, protecting not only their organizations, but their careers as well.
To learn more about cybersecurity and digital transformation, please explore this HPE–FireEye resource website.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.