The 20 Most Infamous Cyberattacks of the 21st Century (Part I)
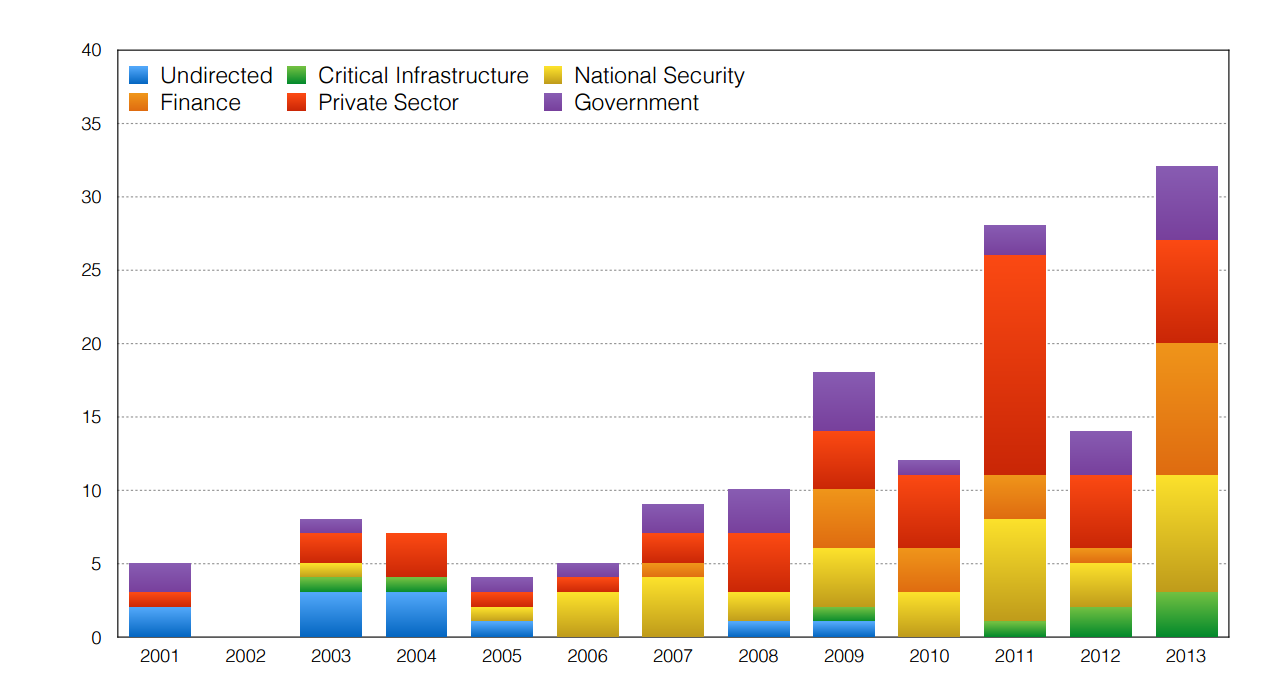
The cyberworld is a dangerous place. But just how dangerous is hard to gauge. Today, Tavish Vaidya at Georgetown University in Washington, D.C., discusses the most egregious attacks of the 21st century and concludes that the trend is increasing sharply. In a two-part post, here are 20 of the most infamous attacks his paper discusses.
20. April 2001: A US Navy EP-3E spy plane collides with a Chinese J-811 fighter jet while operating over the South China Sea near Hainan Island. The pilot of the Chinese plane ejected, was never found and is assumed dead. The American plane was severely damaged and forced to make an emergency landing on Hainan where the Chinese military imprisoned the 24 crew.
The incident led to a month long cyberbattle between U.S. and Chinese hackers in which each defaced government-related websites while blaming each other for causing the air incident.
The US crew was eventually released after the U.S. delivered a letter of regret to the Chinese authorities.
19. April 2007: The Baltic Sea state of Estonia comes under sustained cyberattack from a wide range of botnets from all over the world. Most are denial of service attacks which swamp a server with such a deluge of online requests that it is unable to accept new connections and essentially fails.
The main targets are the websites of the Estonian president, parliament, government ministries, and news organizations. However, various banks are also attacked and one reported a loss of $1 million in the attacks. The country eventually cut itself off from the outside internet to stop the attacks.
The attack came amid growing tension between Estonia and Russia over the relocation of a Soviet-era war graves.
Computer security experts believe Russia was almost certainly responsible although the country denied involvement. In 2009, a Kremlin backed group claimed to responsibility.
18. September 2007: Israeli F-15 and F-16 jets bomb a suspected nuclear weapons plant in Syria having mysteriously evaded the country’s sophisticated Russian air-defense network. Various commentators speculate that Israel hacked this network using a computer program known as Suter designed to bring down enemy communications networks. Suter was developed by BAE Systems and works by bombarding radar facilities with data that contains false targets and misleading messages.
17. August 2008: The Russian army invades neighboring Georgia following a longstanding dispute over the regions of South Ossettia and Abkhazia, which declared independence from Georgia with Russian backing. However, in the weeks before the invasion, numerous Georgian government websites and news sites were disabled by denial of service attacks and also defaced by hackers. The Russian government denied involvement saying that individuals in Russia had had taken it upon themselves to start the attacks.
16. January 2009: Websites belonging to the Israeli Defense Forces and the Israel Discount Bank, are disabled by denial of service attacks and defaced by hackers, along with other sites belonging to small companies and government bodies. The attacks are a protest against Israeli military action in Gaza. Israel blames hackers from the former Soviet Union who had been paid by Palestinian groups such as Hamas or Hezbollah.
15. July 2009: Major government, financial and news websites in South Korea are disabled by denial of service attacks that last for several days. Some sites in the U.S. are also affected. South Korea blames the North Korean telecommunications ministry.
14. Circa 2003: hundreds of networks belonging to NASA and several other U.S. government agencies are breached in a series of coordinated attacks codenamed Titan Rain. The attacks last for three years and also targeted networks belonging to military contractors at several government labs such as Sandia National Laboratories, Lockheed Martin and the Redstone Arsenal. An investigation by the SANS Institute, a security organization in the U.S., reveals that the attacks originated in the Chinese province of Guangdong and were probably the actions of Chinese military hackers.
13. May 2006: Malware delivered via phishing emails targets a zero-day vulnerability in Windows that allows hackers to steal passwords and usernames along with some 20 terabytes of data from the U.S. Defense Information System Agency’s military’s NIPRNet, which carries unclassified military data and is the largest private network in the world.
12. June 2007: The U.S. Department of Defense comes under sustained cyberattack from spoof e-mails that target a vulnerability in the Windows operating system. The attackers steal vast amounts of sensitive data including IDs and passwords that give access to entire classified networks, which then have to be taken off line.
11. March 2009: Reports emerge of a global cyberespionage network known as GhostNet which exploited a vulnerability in Adobe PDF reader to attack embassies and ministries in 103 different countries. The discovery was made after Tibetan officials suspected their computers had been hacked and asked the security organization InfoWar Monitor to investigate. Most GhostNet attacks appear to originate in China.
The second part of this list will appear on Thursday, August 27.
Ref: arxiv.org/abs/1507.06673 : 2001-2013: Survey and Analysis of Major Cyberattacks
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.