How the Next Generation of Botnets Will Exploit Anonymous Networks, and How to Beat Them
Botnets are computer programs that talk to each other over the Internet. Some are entirely benign, like those that control Internet chats. But many botnets are entirely malicious, programs that send spam or participate in denial of service attacks and so on. These networks are controlled by individual criminals who use them for nefarious purposes such as generating illicit income or attacking other websites.
The work of finding and stopping this criminal activity has become a global endeavor. The first generation of botnets was relatively simple to stop. Since they were controlled by a single computer somewhere on the Web, the trick was to find that computer and shut it down.
That was straightforward when the programs themselves contained the information necessary to communicate with the command and control server.
But in recent years, this cat and mouse game has become much more sophisticated. Botnets now routinely take steps to hide the location of the command and control server. One approach, known as fast fluxing, is to create a constant stream of IP addresses and map hundreds or thousands of them simultaneously to a domain name. Anybody hoping to find the command and control server would have to search every IP address before it changes.
More recently, botnets have begun to exploit the Tor network which is designed to allow people to communicate across the Internet anonymously. This, combined with the advent of untraceable electronic currencies such as Bitcoin, has led to the rise of blackmail and ransomware that cannot be traced even after a payment has been made.
Today, Amirali Sanatinia and Guevara Noubir at Northeastern University in Boston say the next generation of botnets is likely to be even more sophisticated. They outline how they believe these botnets will evolve but also suggest a straightforward way to neutralize them.
Sanatinia and Noubir say that the anonymity offered by Tor-like networks will be irresistible to botnet masters, so most innovation will occur in this area. To exploit this anonymity, these botnets will have to exploit a technique called onion routing that encapsulates messages within various layers of encryption, like the layers of an onion.
Each server that the message passes through decrypts a layer of the onion revealing its next destination. When the final layer is revealed, the message has reached its destination. The anonymity comes from the fact that no server along the route knows anything about the message except its next destination.
Sanatinia and Noubir clearly think this level of anonymity will be hard for botnet masters to resist. Consequently, they christen the next generation of botnets that will exploit this OnionBots and spend some time explaining exactly how they will have to work to make best use of onion routing.
That sounds suspiciously like a big step towards disaster—the paper is a useful backgrounder for anyone wanting to set up an OnionBot. However, Sanatinia and Noubir have also found a way to neutralize these kinds of OnionBots.
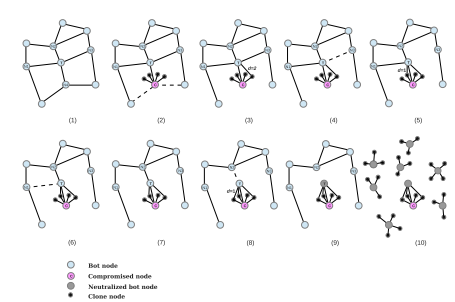
The basic idea is to inject programs into the network that preferentially attach to OnionBots. They then reproduce themselves and effectively surround each OnionBot so it is no longer connected to any other part of the network. When that happens, the OnionBot is isolated and neutralized.
That’s not to say that it is possible to completely protect against an attack of OnionBots. But Sanatinia and Noubir hope to kick-start work on tackling this next generation of bots before it even gets started. “There are still many challenges that need to be preemptively addressed by the security community, we hope that this work ignites new ideas to proactively design mitigations against the new generations of crypto-based botnets,” they say.
It may be a risky strategy to do this so publicly. On the other hand, a public approach may tap into the broadest pool of security talent. Suggestions about how to improve this strategy in the comments section below.
Ref: arxiv.org/abs/1501.03378 : OnionBots: Subverting Privacy Infrastructure for Cyber Attacks
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.