Best of 2012: PlaceRaider: The Military Smartphone Malware Designed to Steal Your Life
“The power of modern smartphones is one of the technological wonders of our age. These devices carry a suite of sensors capable of monitoring the environment in detail, powerful data processors and the ability to transmit and receive information at high rates.
So it’s no surprise that smartphones are increasingly targeted by malware designed to exploit this newfound power. Examples include software that listens for spoken credit card numbers or uses the on-board accelerometers to monitor credit card details entered as keystrokes.
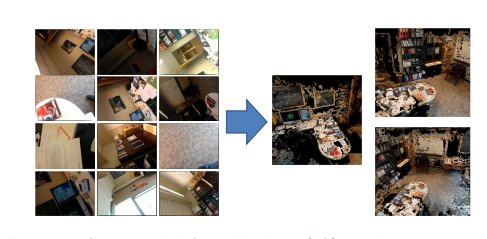
Today Robert Templeman at the Naval Surface Warfare Center in Crane, Indiana, and a few pals at Indiana University reveal an entirely new class of ‘visual malware’ capable of recording and reconstructing a user’s environment in 3D. This then allows the theft of virtual objects such as financial information, data on computer screens and identity-related information.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.