Planetary Pestilence
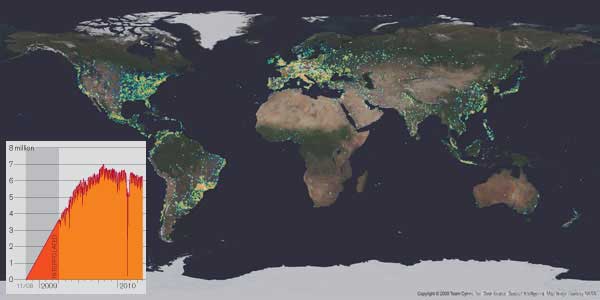
The Conficker worm was first released in November 2008 and later followed up by increasingly sophisticated variants. Targeting a vulnerability in the Microsoft Windows operating system, the worm can spread by means of networks and USB flash drives. Millions of computers were rapidly infected; this map from security firm Team Cymru shows a snapshot of detected infections in January 2009. Since then, Conficker has proved difficult to eradicate. Its resilience is due in part to its ability to disable antivirus software, block users from accessing the websites of security vendors to get new software, and download encrypted updates designed to defeat countermeasures against previous versions of Conficker. Microsoft is offering a $250,000 reward for the identities of the worm’s creators.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.