A Valet Key for Your Identity
As online services that make use of personal data multiply, it’s becoming more common for users to need to pass data from one service to another. This often requires users to hand over usernames and passwords, in spite of the obvious security risks involved. A new open-source project called OAuth, released earlier this month, is intended to solve this problem by allowing users to give services a valet key to their identities, rather than full access.
Chris Messina, who helped organize the production of OAuth, says that the system will “give people control over the way that they broker their data through Web services, and also help them be a little more secure.” The system allows a user to obtain a token through one site and pass it to another. The token then dictates what the second site can access, and in what way. To achieve this, the protocol has to define standard ways for sites to identify data and specify what they’re going to do with it. To work, OAuth requires both sites to have implemented the protocol. The user does not have to be aware of it.
Along with Messina, Blaine Cook of Twitter and Larry Halff of Ma.gnolia worked to start the project.
Handing over usernames and passwords is an increasingly common feature of social-networking sites, including well-known sites such as Facebook and LinkedIn. At the initial sign-up phase, a site asks the user to enter the credentials for her e-mail accounts so that it can search for people she might know. It’s also typical for sites to provide an opportunity for users to invite their existing contacts to join the network as well. But Messina says that there’s another, unintended result of the practice: “It’s training the user to pass around usernames and passwords like confetti,” he says.
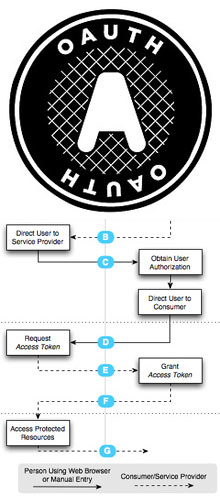
Multimedia
See how OAuth works.
Eran Hammer-Lahav, who served as the editor for the core OAuth specification, says that a cautionary tale came earlier this year when a social-networking site called Quechup used its access to e-mail accounts through this feature to send invitations to every single person in a new user’s contacts list. Even worse, to many people, the e-mails appeared to originate from the user, rather than from the company. Hammer-Lahav says that the warning is directed less at a particular site than at a system that needs improvement. “The core is really about what we call the love triangle,” he says. The love triangle, he explains, is the relationship between the user and the two Web services that need to share data.
He adds that it’s now becoming common for financial-management sites such as Mint to ask for passwords in order to aggregate information for users. In addition to posing a security risk, Hammer-Lahav says, it’s actually not the best way for sites to share information. The aggregator sites often have to scrape financial information off banking pages by training their software to seek certain clues in the page source that signal key pieces of data. The problem, he says, is that if the bank redesigns the look of a page, those clues might change, rendering the aggregator unable to read the information. A system such as OAuth, Hammer-Lahav says, allows the sites to share information directly.
The idea of this type of system is not new, says Terrell Russell, cofounder of the online identity-management system ClaimID. Google, for example, has an existing proprietary protocol that has capabilities similar to those of OAuth. However, Russell says, the lack of a single standard hampers developers and encourages them to ask for usernames and passwords. Russell says that solving the problem of allowing Web services to safely share data will only become more important as more data migrates to the Web.
OAuth is being implemented by Twitter and Ma.gnolia, and portions of the standard appear in Google’s OpenSocial platform. Although the initial release is a core protocol containing the basics of exchanging tokens between sites, Hammer-Lahav says that later releases will give users finer control over how they grant access to their data.
Keep Reading
Most Popular
Large language models can do jaw-dropping things. But nobody knows exactly why.
And that's a problem. Figuring it out is one of the biggest scientific puzzles of our time and a crucial step towards controlling more powerful future models.
The problem with plug-in hybrids? Their drivers.
Plug-in hybrids are often sold as a transition to EVs, but new data from Europe shows we’re still underestimating the emissions they produce.
Google DeepMind’s new generative model makes Super Mario–like games from scratch
Genie learns how to control games by watching hours and hours of video. It could help train next-gen robots too.
How scientists traced a mysterious covid case back to six toilets
When wastewater surveillance turns into a hunt for a single infected individual, the ethics get tricky.
Stay connected
Get the latest updates from
MIT Technology Review
Discover special offers, top stories, upcoming events, and more.